| Microsoft 365 Business Premium Crash Course for Nonprofits Get the e-book Microsoft 365 Business Premium is an integrated solution for small and mid-sized nonprofits that brings together Outlook email, Office desktop applications, OneDrive cloud storage, Teams for digital collaboration, as well as simple device management and advanced security features. Help your nonprofit improve cybersecurity, reduce costs, and empower staff and volunteers to work from anywhere. Download the e-book, Crash Course in Microsoft 365 Business Premium for Nonprofits, and learn how this integrated solution can help you focus on what matters most—your mission. Here are just a few of the topics we’ll cover: Be productive anywhere: Get work done and stay connected with your staff and constituents whether you’re working remotely or onsite. Secure your nonprofit: Safeguard data with a cloud platform that offers built-in security features for remote work. One cost-effective solution: Streamline collaboration tools, IT setup and management, and costs with a single productivity solution. Get started with the Microsoft 365 Business Premium grant For eligible nonprofits, Microsoft 365 Business Premium is free for up to 10 users and discounted pricing of $5.50 (USD) per user/month for additional users. To get started, register and confirm your organization’s eligibility. Already registered as a nonprofit? Login to your Microsoft Nonprofit page and access Admin Center. Watch our guided demo to help you get your free Microsoft 365 licenses. Regards, Microsoft Tech for Social Impact Team |
Month: August 2023
CISA and International Partners Release Malware Analysis Report on Infamous Chisel Mobile Malware
Today, the United Kingdom’s National Cyber Security Centre (NCSC-UK), the United States’ Cybersecurity and Infrastructure Security Agency (CISA), National Security Agency (NSA), and Federal Bureau of Investigation (FBI), New Zealand’s National Cyber Security Centre (NCSC-NZ), Canadian Centre for Cyber Security (CCCS), and the Australian Signals Directorate (ASD) published a joint Malware Analysis Report (MAR), on Infamous Chisel a new mobile malware targeting Android devices with capabilities to enable unauthorized access to compromised devices, scan files, monitor traffic, and periodically steal sensitive information. Infamous Chisel mobile malware has been used in a malware campaign targeting Android devices in use by the Ukrainian military.
Infamous Chisel is a collection of components targeting Android devices and is attributed to Sandworm, the Russian Main Intelligence Directorate’s (GRU’s) Main Centre for Special Technologies, GTsST. The malware’s capability includes network monitoring, traffic collection, network backdoor access via The Onion Router (Tor) and Secure Shell (SSH), network scanning and Secure Copy Protocol (SCP) file transfer.
The authoring organizations urge users, network defenders, and stakeholders to review the malware analysis report for indicators of compromise (IOCs) and detection rules and signatures to determine system compromise. For more information about malware, see CISA’s Malware, Phishing, and Ransomware page. The joint MAR can also be read in full on the NCSC-UK website. Associated files relating to this report can also be accessed via the NCSC’s Malware Analysis Reports page. For more information on Russian state-sponsored cyber activity, please see CISA’s Russia Cyber Threat Overview and Advisories webpage.
Identification and Disruption of QakBot Infrastructure
| The Cybersecurity and Infrastructure Security Agency (CISA) and Federal Bureau of Investigation (FBI) released this Joint Cybersecurity Advisory to disseminate QakBot infrastructure indicators of compromise (IOCs) identified through FBI investigations as of August 2023. On August 25, FBI and international partners executed a coordinated operation to disrupt QakBot infrastructure worldwide. Disruption operations targeting QakBot infrastructure resulted in the botnet takeover, which severed the connection between victim computers and QakBot command and control (C2) servers. The FBI is working closely with industry partners to share information about the malware to maximize detection, remediation, and prevention measures for network defenders. |
| CISA and FBI encourage organizations to implement the recommendations in the mitigations section of the advisory to reduce the likelihood of QakBot-related activity and promote identification of QakBot-facilitated ransomware and malware infections. Note: The disruption of QakBot infrastructure does not mitigate other previously installed malware or ransomware on victim computers. If potential compromise is detected, administrators should apply the incident response recommendations included in this advisory and report key findings to a local FBI Field Office or CISA at cisa.gov/report. |
| For a downloadable copy of IOCs, see: AA23-242A.stix.xml | AA23-242A.stix.json. |
| This advisory contains technical details, IOCs, mitigation recommendations, and is being provided to assist agencies and organizations in guarding against the persistent malicious actions of cybercriminals. |
Strategies for the Integration of Software Supply Chain Security in DevSecOps CI/CD Pipelines: NIST SP 800-204D ipd Available for Comment
The initial public draft (ipd) of NIST Special Publication (SP) 800-204D, Strategies for the Integration of Software Supply Chain Security in DevSecOps CI/CD Pipelines, is now available for public comment.
Cloud-native applications are made up of multiple loosely coupled components called microservices. This class of applications is generally developed through an agile software development life cycle (SDLC) paradigm called DevSecOps, which uses flow processes called continuous integration/continuous delivery (CI/CD) pipelines. Analyses of recent software attacks and vulnerabilities have led both government and private-sector organizations to focus on the activities involved in the entire SDLC. The collection of these activities is called the software supply chain (SSC). The integrity of these individual operations contributes to the overall security of an SSC, and threats can arise from attack vectors unleashed by malicious actors as well as defects introduced when due diligence practices are not followed during the SDLC.
Executive Order (EO) 14028, NIST’s Secure Software Development Framework (SSDF), other government initiatives, and industry forums have addressed security assurance measures for SSCs to enhance the security of all deployed software. This document focuses on actionable measures to integrate the various building blocks of SSC security assurance into CI/CD pipelines to prepare organizations to address SSC security in the development and deployment of their cloud-native applications.
The public comment period is open through October 13, 2023. See the publication details for a copy of the draft and instructions for submitting comments.
NOTE: A call for patent claims is included on page ii of this draft. For additional information, see the Information Technology Laboratory (ITL) Patent Policy – Inclusion of Patents in ITL Publications.
Read More
Proposal to Revise SP 800-38D, “Recommendation for Block Cipher Modes of Operation: Galois/Counter Mode (GCM) and GMAC
NIST’s Crypto Publication Review Board announced the review of SP 800-38D, Recommendation for Block Cipher Modes of Operation: Galois/Counter Mode (GCM) and GMAC (2007) in August 2021. In response, NIST received public comments.
NIST proposes revising SP 800-38D to address many of the technical and editorial suggestions in the public comments, such as the following:
- to remove support for authentication tags whose lengths are less than 96 bits,
- to clarify that the construction of initialization vectors (IVs) for GCM in the Transport Layer Security (TLS) 1.3 protocol is approved,
- to clarify the guidance in connection with the IV constructions, and
- to update the references.
Send comments on this decision proposal by October 9, 2023 to cryptopubreviewboard@nist.gov with “Comments on SP 800-38D decision proposal” in the subject line.
Comments received in response to this request will be posted on the Crypto Publication Review Project site after the due date. Submitters’ names and affiliations (when provided) will be included, while contact information will be removed. See the project site for additional information about the review process.
Rationale
The Galois/Counter Mode specified in SP 800-38D continues to be an important, widely adopted technique for authenticated encryption. Its security depends strongly on the provision of IVs that are not repeated for distinct messages, as well as the length of the authentication tag. The planned changes to the publication will improve the security of GCM and clarify that the construction of IVs for GCM in TLS 1.3 is approved.
Read More
NIST Announces First Four Quantum-Resistant Cryptographic Algorithms
NIST has chosen the first group of encryption tools that are designed to withstand the assault of a future quantum computer, which could potentially crack the security used to protect privacy in the digital systems we rely on every day — such as online banking and email software.
Read More
NIST to Standardize Encryption Algorithms That Can Resist Attack by Quantum Computer
Last year, the National Institute of Standards and Technology (NIST) selected four algorithms designed to withstand attack by quantum computers. Now the agency has begun the process of standardizing these algorithms — the final step before making these mathematical tools available so that organizations around the world can integrate them into their encryption infrastructure.
Today NIST released draft standards for three of the four algorithms it selected in 2022. A draft standard for FALCON, the fourth algorithm, will be released in about a year.
Access Resources for Cybersecurity Career Week
| Cybersecurity Career Week October 16-21, 2023 nist.gov/nice/ccw |
| Cybersecurity Career Week is a campaign to promote the discovery of cybersecurity careers and share resources that increase understanding of the multiple learning pathways that lead to those careers. |
| ATTEND THE INFORMATIONAL WEBINAR |
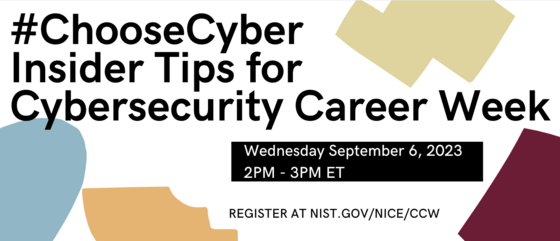 There is still time to register! Join us next week Wednesday, September 6, 2023, for an informational webinar and question and answer session about Cybersecurity Career Week. We will share topics, example activities, and advice on what you can do to prepare for and participate in Cybersecurity Career Week 2023. Register to Attend There is still time to register! Join us next week Wednesday, September 6, 2023, for an informational webinar and question and answer session about Cybersecurity Career Week. We will share topics, example activities, and advice on what you can do to prepare for and participate in Cybersecurity Career Week 2023. Register to Attend |
| BROWSE ON-DEMAND MATERIALS |
| DID YOU KNOW |
 Did you know that roles in Data Analysis are among the highest in-demand cybersecurity jobs? That’s right! Skills such as generating queries and reports, determining sources and characteristics of data, and even identifying hidden patterns or relationships are commonly used in these roles. Want to learn more? The NICE Framework Data Analyst Work Role has more information about typical tasks someone in this role is responsible for. Cybersecurity Career Week is coordinated by NICE and supported by a community of government, academic, non-profit, and private industry stakeholders. Commercial entities, materials, and resources provided in support of Cybersecurity Career Week may be included in this email or on the nist.gov/nice/ccw web site or linked web sites. Such identification is not intended to imply recommendation or endorsement by NIST. Did you know that roles in Data Analysis are among the highest in-demand cybersecurity jobs? That’s right! Skills such as generating queries and reports, determining sources and characteristics of data, and even identifying hidden patterns or relationships are commonly used in these roles. Want to learn more? The NICE Framework Data Analyst Work Role has more information about typical tasks someone in this role is responsible for. Cybersecurity Career Week is coordinated by NICE and supported by a community of government, academic, non-profit, and private industry stakeholders. Commercial entities, materials, and resources provided in support of Cybersecurity Career Week may be included in this email or on the nist.gov/nice/ccw web site or linked web sites. Such identification is not intended to imply recommendation or endorsement by NIST. |
| INFORMATION AND UPDATES |
NIST Workshop on Multi-party Threshold Schemes (MPTS) 2023, September 26th–28th (Virtual)
NIST Workshop on Multi-party Threshold Schemes (MPTS) 2023, September 26th–28th (Virtual)
- What: MPTS 2023 (Virtual): NIST Workshop on Multi-Party Threshold Schemes
- Date & time: 2023-September-26–28, 10:00–15:00 (Eastern Time)
- Featured topics: The NIST First Call for Multi-Party Threshold Schemes (NISTIR 8214C)
- Featured topics: Threshold cryptography; threshold schemes; multi-party computation (MPC); fully-homomorphic encryption (FHE); zero-knowledge proofs (ZKP); attribute-based encryption (ABE); MPC/FHE/ZKP-friendly primitives; useful gadgets.
- Presentations: There is a call for presentation abstracts (deadline 2023-September-05)
- Workshop format: Three days of webinars for feedback about the Threshold Call and Process
- Detailed info: https://csrc.nist.gov/events/2023/mpts2023
- Contacts about the workshop: workshop-mpts2023@nist.gov
- Free registration (via Webex): https://nist-secure.webex.com/webappng/sites/nist-secure/webinar/webinarSeries/register/ceb61702e61047a7ad27c00f11fbaa94
- Tweet: https://twitter.com/NISTcyber/status/1691816957128200595
- Host: Multi-Party Threshold Cryptography (MPTC) and Privacy-Enhancing Cryptography (PEC) projects @ NIST Cryptographic Technology Group (CTG)
- Public-Forums: For future related announcements, join the “MPTC-Forum” and the “PEC-forum” mailing lists.
MPTS 2023: The NIST workshop on Multi-Party Threshold Schemes 2023 will gather diverse public feedback about the process envisioned in the NIST First Call for Multi-Party Threshold Schemes [NISTIR 8214C ipd (2023)] (the “Threshold Call”). The process includes an exploration of threshold schemes for diverse cryptographic primitives standardized by NIST, and of other primitives (such as those related to FHE, ZKP and ABE) and assumptions not present in current NIST standards. The success of the envisioned process (collecting reference material, performing public analysis, devising recommendations) hinges on active involvement of the international cryptography community. To that effect, expert stakeholders are encouraged to submit abstracts of short talks (5–15 min) to present at MPTS 2023. Attendance is open to the wider community of stakeholders and people interested in the topic. Live attendance is free but requires registration.
Building a Cybersecurity and Privacy Learning Program: NIST Releases Draft SP 800-50 Rev. 1
Draft NIST Special Publication (SP) 800-50r1 (Revision 1), Building a Cybersecurity and Privacy Learning Program, is now available for public comment. The document was first published in 2003 as Building an Information Technology Security Awareness and Training Program. The public comment period for this draft is open through October 27, 2023.
About NIST SP 800-50r1:
Cybersecurity awareness and training resources, methodologies, and requirements have evolved since NIST SP 800-50 was introduced in 2003. New guidance from the National Defense Authorization Act (NDAA) for FY2021 and the Cybersecurity Enhancement Act of 2014 have informed this revision. In addition, the 2016 update to Office of Management and Budget (OMB) Circular A-130 emphasizes the role of both privacy and security in the federal information life cycle and requires agencies to have both security and privacy awareness and training programs. Additionally, the NICE Workforce Framework for Cybersecurity (NICE Framework), which was published as NIST SP 800-181 in 2017 and revised in 2020, further informed the development of the draft of SP 800-50.
Work on a companion guide — NIST SP 800-16r3, Information Technology Security Training Requirements: A Role- and Performance-Based Model — will cease and the original NIST SP 800-16 (1998) will be withdrawn with the final publication of NIST SP 800-50r1.
Goals of this update:
- Integrate privacy with cybersecurity in the development of organization-wide learning programs
- Introduce a life cycle model that allows for ongoing, iterative improvements and changes to accommodate cybersecurity, privacy, and organization-specific events
- Introduce a learning program concept that incorporates language found in other NIST documents
- Leverage current NIST guidance and terminology in reference documents, such as the NICE Workforce Framework for Cybersecurity, the NIST Cybersecurity Framework, the NIST Privacy Framework, and the NIST Risk Management Framework
- Propose an employee-focused cybersecurity and privacy culture for organizations
- Integrate learning programs with organizational goals to manage cybersecurity and privacy risks
- Address the challenge of measuring the impacts of cybersecurity and privacy learning programs
Submit comments:
The public comment period is open through October 27, 2023. See the publication details for a copy of the draft and instructions for submitting comments.