Title:
Announcing Exciting Updates to Attack Simulation Training
URL: https://techcommunity.microsoft.com/t5/security-compliance-and-identity/announcing-exciting-updates-to-attack-simulation-training/ba-p/2455961
Date Published 06/17/2021
Overview:
Simulation
Automations
The modern enterprise, of any size, faces a challenge that the logistics
involved in planning a phishing simulation exercise are often laborious and
time-consuming to implement. So to help address this we are pleased to announce
some extra functionality in Attack Simulation Training that we feel will bring
some added benefits in this space by:
- Helping move away from the traditional approach of
running quarterly or annual simulations, to a more always on ‘educating’
model, by scheduling simulations to launch at a higher frequency (being
mindful of simulation and training fatigue of course).
- Letting you schedule simulations up to a year in
advance, so you decide the parameters of your simulations once in advance
then you are good to go.
- Introducing some randomization elements around send
times and dates to help combat the crowdsource effect that can occur when
running large simulation exercises.
You can access the new functionality by selecting the “Simulation
automations” tab within the main experience.
When you create a simulation automation, the experience walks you through a
wizard experience just like creating a manual simulation, with the addition of
a few new steps.
- Payload selection – Here we allow you to manually select
what payloads you would like to be in scope for the simulations, or
alternatively you can opt to randomize, where we will take a random
payload from the available library and use that.
- Simulation schedule – Here, you get to decide if you
would like a randomized schedule or a more predictable fixed schedule.
What is the difference?
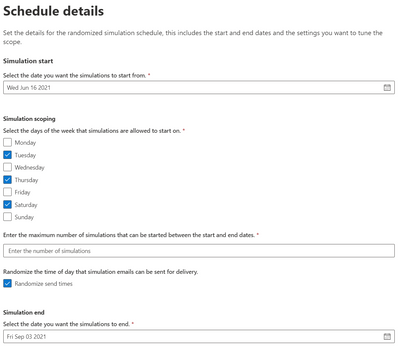
A randomized schedule
lets you select a start date and end date, the days of the week you would like
to be in scope for delivery and after how many simulation launches would you
like the automation to stop.
Once the automation is enabled, the simulations will be launched on random
days between the dates you have specified. You can also choose to randomize the
send times (to negate the water cooler effect of users receiving simulation
messages at the same time and chatting about it).
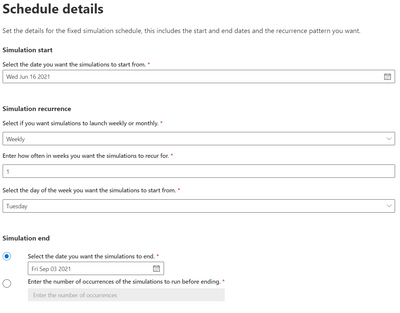
A fixed
schedule allows you to run automations in a more controlled manner. We take the
same approach – you specify a start date and end date – however this time you
are prompted to enter the cadence, either weekly or monthly and the parameters
of how often you would like them to launch.
For example, you can schedule an automation to run once a week for a period
of 7 weeks starting every Monday, or you can also opt to end the simulations by
a particular date or after a specific number of occurrences that you define.
Government Cloud
and Regional Availability Updates
Attack Simulation
Training is now live in GCC:
Starting 15 June 2021, Attack Simulation Training will be generally
available in our Government Community Cloud. If your organization has Office
365 G5 GCC or Microsoft Defender for Office 365 (Plan 2) for Government, you
can use Attack Simulation Training in Microsoft 365 Defender to run realistic
attack scenarios in your organization as described here. Please note that the service is not yet available in
GCC-High or DoD environments and this is part of our future roadmap.
Attack Simulation
Training is now live in new regions:
Starting 16 June 2021, Attack Simulation Training will be generally
available to tenants in Latin America, Brazil, and Switzerland that have
Microsoft 365 E5 or Microsoft Defender for Office 365 Plan 2. For any guidance
on running simulations, please start here. For frequently asked questions, please refer to our FAQ page.
We hope you find the enhancements useful as you continue your journey of
end-user education and behavior change. If you have any comments or feedback be
sure to let us know.