We recently published two solutions in the Sentinel content hub catalog to assist you with better detecting threats and misconfigurations of your Exchange environment. One solution is focused on on-premises Exchange Server and the second is for Exchange Online. Both solutions can be used simultaneously when you have a hybrid Exchange environment.
Why now?
In the past years, we have seen an increase in attacks against messaging environments. Taking control of an Exchange Server or abusing someone’s mailbox can have catastrophic consequences for your organization. Analyzing previous Exchange security incidents highlighted that there are detection gaps and common misconfigurations. Both of which could have easily been avoided. When it comes to Exchange on-premises deployments, it is common to see configurations which have grown organically through upgrades and various administrators. Management and administrative practices may also not have kept pace with threat actors and have not changed in decades. Many configuration components are simply overlooked. Logs are rarely collected and centralized, either slowing or preventing investigations.
Introducing Microsoft Exchange Security solutions
The two solutions aim to close detections gaps and proactively identifying misconfigurations before they become a security incident. They allow collections of critical logs, detect misconfigurations and present the information in dynamic dashboards.
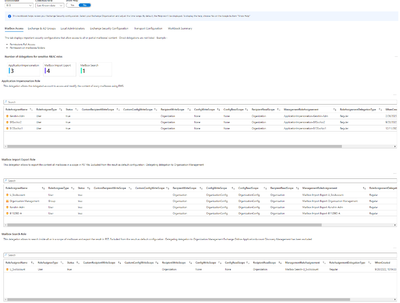
The Exchange Server solution looks at the following core components:
- standard and custom RBAC delegation
- remote domain configuration
- local administrators permissions
- high privileged groups members
- POP/IMAP configuration
- send and receive connector configuration
The Exchange Online solution looks at the following core components:
- standard and custom RBAC delegation
Amongst the scenarios the solution enables, you will find the following:
- Alert you when an administrative cmdlet is executed against a VIP user to exfiltrate content or modify who can access it (you decide who are the VIPs).
- Detect if a server-oriented cmdlet and a user-oriented cmdlet which are monitored are launched by the same user on the same server in 10 minutes delay.
- Improve your Exchange security posture by exposing misconfiguration on your Exchange environments.
- Detect the usage of custom Exchange RBAC configuration that can put your environment at risk.
- Report on admin activities to optimize your delegation model.
How does it work?
The base of the solution uses a script which directly connects to Microsoft Sentinel and uploads the results of security configurations (this script runs on-premises for the on-premises version, and in an Azure Automation runbook for the online version). It uses the Log Analytics ingestion API to directly send data to your Sentinel workspace.
Note that the solution does support the collection of multiple Exchange organizations and multi-tenants within the same Sentinel workspace.
You can also configure the solution to upload additional data such as audit logs, security events of Exchange servers and/or domain controllers and IIS log files by using either the Azure Monitoring Agent with Azure Arc or the Microsoft Monitoring Agent
- You can then explore the data with carefully crafted workbooks to visualize your posture and trigger incidents with analytics rules to alert you to important security events.
Your Exchange security posture quickly visualized:
A workbook helping you to apply the Least Privilege principle:
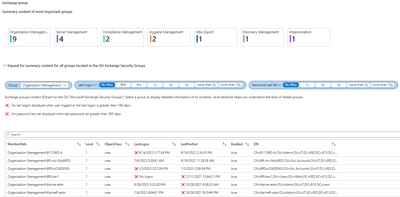
To monitor activities on mailboxes and especially on designated VIP mailboxes:

Data ingestion
To keep the solution cost effective, you can select the level of data you wish to collect from your environment. The more data you collect and the more detection scenarios you enable. To help you pick the right collection level, you can refer to this table:
| Collection option | Data to upload | Volume | Valuable for workbooks | Valuable for hunting |
| 0 | Configuration scripts result | Low | High | Low |
| 1 | Exchange related event logs of Exchange servers | Medium | Medium | Medium |
| 2 | Security/Application/System event logs of Exchange servers | Medium | Low to Medium | Medium |
| 3 | Security logs of domain controllers located in the Exchange sites | Medium to High | Low to Medium | Medium |
| 4 | Security logs of all domain controllers | High | Low to Medium | Medium to High |
| 5 | IIS logs of Exchange servers | High | Low | High |
| 6 | Message tracking of all Exchange servers | High | Low | Low to Medium |
| 7 | HTTP proxy logs of all Exchange servers | High | High | High |
Except for collection option 0, all other options are independent. They are deployed as a Microsoft Sentinel Connector using DCR rules or Azure Monitor Agent and you can activate/deactivate the options when you want.
Get started!
Connect to your Microsoft Sentinel workspace, click on the Content hub blade and search for Microsoft Exchange Security:
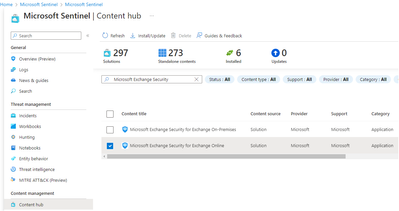
Review the details and click Install to get started!
Alternatively, you can navigate to the respective solutions landing page in Azure: