If you own a computer, watch the news, or spend virtually any time
online these days you have probably heard the term “phishing.” Never in a
positive context…and possibly because you have been a victim yourself.
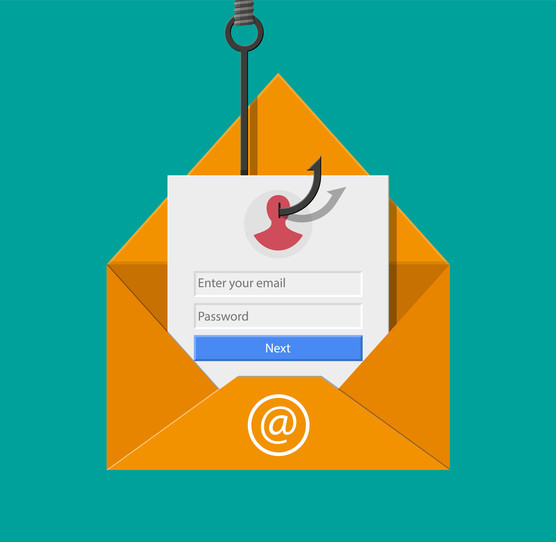
Phishing refers to a variety of attacks that are intended to convince
you to forfeit sensitive data to an imposter. These attacks can take a number of
different forms; from spear-phishing (which targets a specific individual within
an organization), to whaling (which goes one step further and targets senior
executives or leaders). Furthermore, phishing attacks take place over multiple
channels or even across channels; from the more traditional email-based attacks
to those using voice – vishing – to those coming via text message – smishing.
Regardless of the type or channel, the intent of the attack is the same – to
exploit human nature to gain control of sensitive information (citation
1). These attacks typically make use of several techniques including
impersonated websites, attacker-in-the-middle, and relay or replay to achieve
their desired outcome.
|