In this talk, Microsoft and LinkedIn analysts detail recent activity of a North-Korea based nation-state threat actor we track as ZINC. Analysts detailed the findings of their investigation (previously covered in this blog) and walked through the series of observed ZINC attacks that targeted 125 different victims spanning 34 countries, noting the attacks appear to be motivated by traditional cyber-espionage and theft of personal and corporate data. A few highlights include:
- In September 2022, Microsoft disclosed detection of a wide range of social engineering campaigns using weaponized legitimate open-source software. MSTIC observed activity targeting employees in organizations across multiple industries including media, defense and aerospace, and IT services in the US, UK, India, and Russia.
- Based on the observed tradecraft, infrastructure, tooling, and account affiliations, MSTIC attributes this campaign with high confidence to ZINC, a state-sponsored group based out of North Korea with objectives focused on espionage, data theft, financial gain, and network destruction.
- When analyzing the data from an industry sector perspective, we observed that ZINC chose to deliver malware most likely to succeed in a specific environment, for example, targeting IT service providers with terminal tools and targeting media and defense companies with fake job offers to be loaded into weaponized PDF readers.
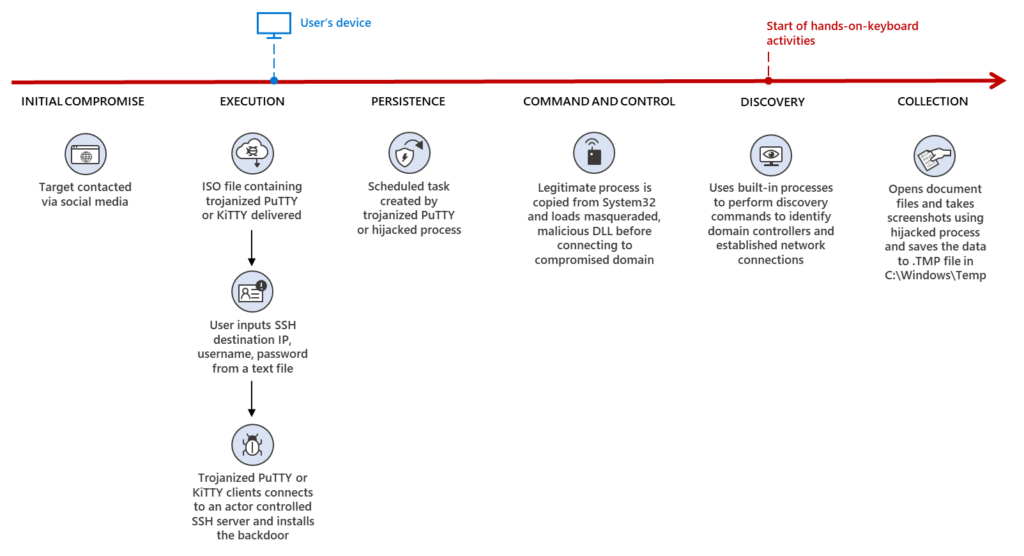
- ZINC has successfully compromised numerous organizations since June 2022, when the actor began employing traditional social engineering tactics by initially connecting with individuals on LinkedIn to establish a level of trust with their targets.
- Upon successful connection, ZINC encouraged continued communication over WhatsApp, which acted as the means of delivery for their malicious payloads. MSTIC observed ZINC weaponizing a wide range of open-source software including PuTTY, KiTTY, TightVNC, Sumatra PDF Reader, and muPDF/Subliminal Recording software installer for these attacks. ZINC was observed attempting to move laterally across victim networks and exfiltrate collected information from.