This is an article from Microsoft that i thought was intresting..
Anyone may receive an unwanted phone call or experience a pop-up window on your device with a “warning” that your computer has a problem requiring immediate tech support. These messages are often very convincing and use scare tactics to entice consumers into contacting a fraudulent “tech support” call center. Call center operators typically encourage the victim to provide remote access to their device for “further diagnosis” before charging the victim a fee – typically between $150 – $499 – for unnecessary tech support services. In addition to losing money, victims leave their computer vulnerable to other attacks, such as malware, during a remote access session.
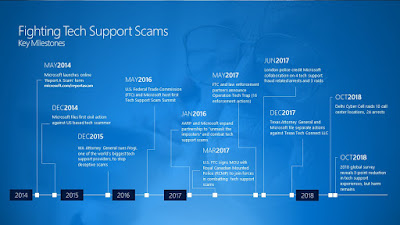
Tech support fraud operations typically involve multiple entities including those engaged in marketing, payment processing and call centers. Recent law enforcement successes in India build on a solid track record of global law enforcement taking action to combat the multiple layers of tech support fraud supported by referrals from Microsoft and other industry partners. For example, the U.S. Federal Trade Commission and multiple partners announced 16 separate civil and criminal enforcement actions against tech support fraudsters in May 2017 as part of “Operation Tech Trap.” And, in June 2017, the City of London Police announced the arrest of four individuals engaged in computer software services fraud.
Our work to partner with law enforcement agencies in addressing this problem is driven by a combination of technology and action taken by our customers. In 2014, Microsoft launched an online “report a scam” portal to enable victims to share their tech support fraud experiences directly with our Digital Crimes Unit team. The reports have been a critical starting point for our international investigations and referrals. Our data analytics and innovation team has added additional tools to proactively hunt and pull data from approximately 150,000 suspicious pop-ups daily targeting millions of people and use machine learning to identify those related to tech support fraud.
In addition to making referrals to law enforcement based on this data, we are building what we learn about cybercriminals’ behavior into improved products and services for consumers. Microsoft has built-in protection in Windows 10 which includes more security features, safer authentication and ongoing updates delivered for the supported lifetime of a device. Windows Defender delivers comprehensive, real-time protection against software threats across email, cloud and the web. The SmartScreen filter, built into Windows, Microsoft Edge and Internet Explorer, helps protect against malicious websites and downloads, including many of those frustrating pop-up windows. People who have experienced tech support scams should know they aren’t alone, but there are steps you can take to identify and help defend yourself against criminals looking to impersonate legitimate companies. According to our recently released 2018 global survey, three out of five consumers have experienced a tech support scam in the previous 12 months. Although this reflects movement in the right direction, and a 5-point reduction since 2016, these scams persist and successfully target people across all ages and geographies. The best thing you can do to help protect yourself from fraud is to educate yourself. If you receive a notification or call from someone claiming to be from a reputable software company, here are a few key tips to keep in mind:
- Be wary of any unsolicited phone call or pop-up message on your device.
- Microsoft will never proactively reach out to you to provide unsolicited PC or technical support. Any communication we have with you must be initiated by you.
- Do not call the phone number in a pop-up window on your device and be cautious about clicking on notifications asking you to scan your computer or download software. Many scammers try to fool you into thinking their notifications are legitimate.
- Never give control of your computer to a third party unless you can confirm that it is a legitimate representative of a computer support team with whom you are already a customer.
- If skeptical, take the person’s information down and immediately report it to your local authorities