|
|
|
|
|
|
|
|
|
|
|
|
Here is a site to help you expand your expertise, learn new skills. This site has training for IT, Devs., and business folks
There lots of content here for you. Go here
The National Cybersecurity Center of Excellence (NCCoE) has
released the preliminary draft of NIST Special Publication (SP) 1800-36A:
Executive Summary, Trusted
Internet of Things (IoT) Device Network-Layer Onboarding and Lifecycle
Management. The public comment period for the draft is open
until February 3, 2023.
Provisioning network credentials to IoT devices in an untrusted
manner leaves networks vulnerable to having unauthorized IoT devices connect to
them. It also leaves IoT devices vulnerable to being taken over by unauthorized
networks. Instead, trusted, scalable, and automatic mechanisms are needed to
safely manage IoT devices throughout their lifecycles, beginning with secure
ways to provision devices with their network credentials—a process known as trusted network-layer onboarding.
Trusted network-layer onboarding, in combination with additional device
security capabilities such as device attestation, application-layer onboarding,
secure lifecycle management, and device intent enforcement could improve the
security of networks and IoT devices.
This draft practice guide aims to demonstrate how organizations
can protect both their IoT devices and their networks. The NCCoE is
collaborating with product and service providers to produce example
implementations of trusted network-layer onboarding and capabilities that
improve device and network security throughout the IoT-device lifecycle to
achieve this.
The public comment period for the draft is open now until February
3, 2023. See the publication details for a copy of the draft publication
and comment instructions.
Industrial Advisory
|
Do you want to understand how you can manage multi-cloud environments with ease, then don’t miss this stream, “Overview of Entra Permissions Management.” https://lnkd.in/gAvuwYBU
Microsoft has a bunch of content around Entra Permission Management
here are some links
Kick-Off Blog: https://425.show/epm-blog
Microsoft Entra Permissions Management: Walk Through Demo: https://425.show/epm-click-thru
Microsoft Entra Permissions Management: Documentation: https://425.show/epm-docs
FREE TRAINING Microsoft training for Security Engineers
Secure your systems and protect your data
You’re responsible for the design and implementation of digital security controls, managing access, and protecting your data in cloud networks and hybrid environments. Get the skills and knowledge needed to build your career as a successful Security Engineer. To learn more, go here.
The Mobile Device Security Team at NIST’s National
Cybersecurity Center of Excellence (NCCoE) has published the
second draft of Special Publication 1800-22 Mobile Device Security: Bring
Your Own Device (BYOD) and is seeking the public’s comments on its
contents. Many organizations now support their employees’ use of personal
mobile devices to remotely perform work-related activities.
This increasingly common practice, known as BYOD, provides
employees with increased flexibility to telework and access organizational
information resources. Helping to ensure that an organization’s data is
protected when it is accessed from personal devices, while also protecting the
privacy needs of employees, poses unique challenges and threats.
The goal of this practice guide is to provide an example solution
that helps organizations use both a standards-based approach and commercially
available technologies to help meet their security and privacy needs when
permitting personally owned mobile devices to access enterprise resources.
Please review the second draft, which includes new updates to the
iOS BYOD implementation, and submit comments online on or before January 13th, 2023.
Visit the mobile device security page to submit your comments here.
We welcome your input and look forward to your comments. We invite
you to join our Community of Interest to receive news and updates about this
project by signing up on our website here.
– The Mobile Device Security Team
Vulnerabilities in network components, architecture files, and developer tools have become increasingly popular attack vectors to gain access into secure networks and devices. External tools and products that are managed by vendors and developers can pose a security risk, especially to targets in sensitive industries. Attacks on software and hardware supply chains, like Log4J and SolarWinds, have highlighted the importance of visibility across device components and proactively securing networks. A report published by Recorded Future in April 2022 detailed suspected electrical grid intrusion activity and implicated common IoT devices as the vector used to gain a foothold into operational technology (OT) networks and deploy malicious payloads. While investigating the attack activity, Microsoft researchers identified a vulnerable component on all the IP addresses published as IOCs and found evidence of a supply chain risk that may affect millions of organizations and devices.
We assessed the vulnerable component to be the Boa web server, which is often used to access settings and management consoles and sign-in screens in devices. Despite being discontinued in 2005, the Boa web server continues to be implemented by different vendors across a variety of IoT devices and popular software development kits (SDKs). Without developers managing the Boa web server, its known vulnerabilities could allow attackers to silently gain access to networks by collecting information from files. Moreover, those affected may be unaware that their devices run services using the discontinued Boa web server, and that firmware updates and downstream patches do not address its known vulnerabilities.
In this blog, we detail the risks affiliated with vulnerable components, highlighting the Boa web server, and how we suspect these components could be exploited to target critical industries. We also discuss the difficulties with identifying these components in device supply chains. To provide comprehensive protection against such attacks, we offer detection information to identify vulnerable components and guidance for organizations and network operators to improve their security posture.
The attack detailed in the Recorded Future report was one of several intrusion attempts on Indian critical infrastructure since 2020, with the most recent attack on IT assets confirmed in October 2022. Microsoft assesses that Boa servers were running on the IP addresses on the list of IOCs published by Recorded Future at the time of the report’s release and that the electrical grid attack targeted exposed IoT devices running Boa.
Microsoft further identified that half of the IP addresses published by Recorded Future returned suspicious HTTP response headers, which might be associated with the active deployment of the malicious tool identified by Recorded Future. The combination of Boa and suspicious response headers was identified on another set of IP addresses, displaying similar behavior to those found by Recorded Future. While these IP addresses are not confirmed as malicious, we recommend they be monitored to ensure no additional suspicious activity. Users of Microsoft Defender Threat Intelligence will find these IP addresses in the portal labeled as block-listed or suspicious:
Investigating the headers further indicated that over 10% of all active IP addresses returning the headers were related to critical industries, such as the petroleum industry and associated fleet services, with many of the IP addresses associated to IoT devices, such as routers, with unpatched critical vulnerabilities, highlighting an accessible attack vector for malware operators. Most of the suspicious HTTP response headers were returned over a short timeframe of several days, leading researchers to believe they may be associated with intrusion and malicious activity on networks.
Since the report’s publication, Microsoft researchers tracking the published IPs hosts have observed that all IP addresses have been compromised by a variety of attackers employing different malicious methods. For example, some of the IP addresses were further leveraged to download a variant of the Mirai malware family shortly following the report’s release. Microsoft also found evidence that across different devices on the IP addresses, there were attempts to connect with default credentials through brute force methods and attempts to run shell commands. Microsoft continues to see attackers attempting to exploit Boa vulnerabilities beyond the timeframe of the released report, indicating that it is still targeted as an attack vector.
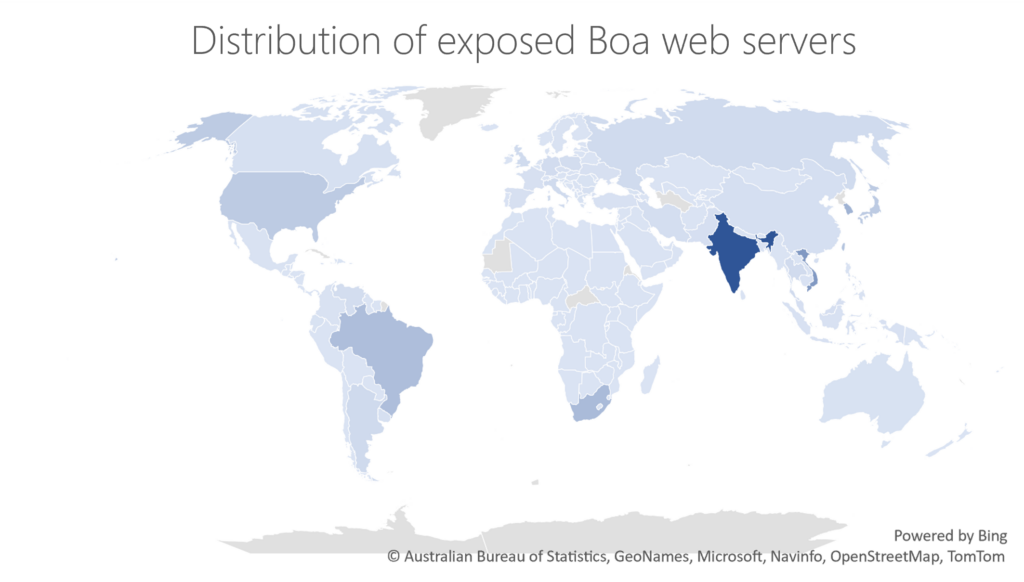
The Boa web server is widely implemented across a variety of devices, including IoT devices ranging from routers to cameras, and is often used to access settings and management consoles as well as sign-in screens. The popularity of Boa web servers is especially concerning as Boa has been formally discontinued since 2005. Data from the Microsoft Defender Threat Intelligence platform identified over 1 million internet-exposed Boa server components around the world over the span of a week, as depicted in the below figure:
Boa web servers remain pervasive in the development of IoT devices, one reason for this could be its inclusion in popular SDKs, which contain essential functions that operate system on chip (SOC) implemented in microchips. Vulnerable components like Boa and SDKs are often distributed to customers within devices, contributing to supply chain vulnerabilities. Popular SDKs like those released by RealTek, are used in SOCs provided to companies that manufacture gateway devices like routers, access points, and repeaters. Critical vulnerabilities such as CVE-2021-35395, which affected the digital administration of devices using RealTek’s SDK, and CVE-2022-27255, a zero-click overflow vulnerability, reportedly affect millions of devices globally and allow attackers to launch code, compromise devices, deploy botnets, and move laterally on networks.
While patches for the RealTek SDK vulnerabilities are available, some vendors may not have included them in their device firmware updates, and the updates do not include patches for Boa vulnerabilities. Boa servers are affected by several known vulnerabilities, including arbitrary file access (CVE-2017-9833) and information disclosure (CVE-2021-33558). These vulnerabilities may allow attackers to execute code remotely after gaining device access by reading the “passwd” file from the device or accessing sensitive URIs in the web server to extract a user’s credentials. Moreover, these vulnerabilities require no authentication to exploit, making them attractive targets.
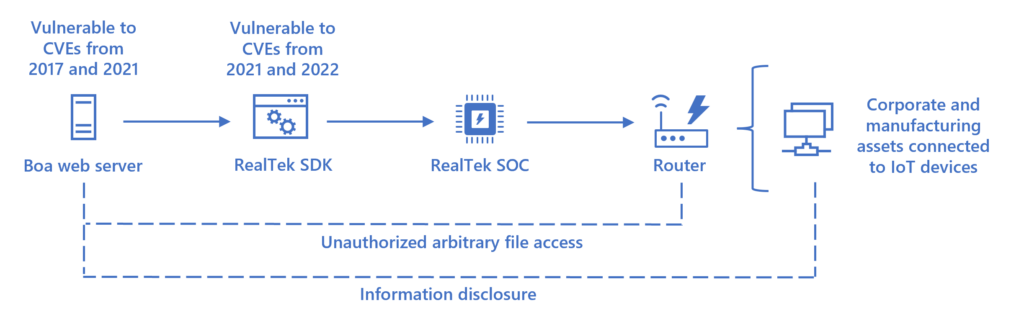
The popularity of the Boa web server displays the potential exposure risk of an insecure supply chain, even when security best practices are applied to devices in the network. Updating the firmware of IoT devices does not always patch SDKs or specific SOC components and there is limited visibility into components and whether they can be updated. The known CVEs impacting such components can allow an attacker to collect information about network assets before initiating attacks, and to gain access to a network undetected by obtaining valid credentials. In critical infrastructure networks, being able to collect information undetected prior to the attack allows the attackers to have much greater impact once the attack is initiated, potentially disrupting operations that can cost millions of dollars and affect millions of people.
As attackers seek new footholds into increasingly secure devices and networks, identifying and preventing distributed security risks through software and hardware supply chains, like outdated components, should be prioritized by organizations. This case displays the importance of proactive cyber security practices and the need to identify vulnerable components that may be leveraged by attackers.
Microsoft recommends that organizations and network operators follow best practice guidelines for their networks:
alert udp any any -> any any (msg:"Realtek eCOS SDK SIP Traffic Exploit CVE-2022-27255"; content: "invite"; depth: 6; nocase; content: "sip:"; content: "m=audio "; isdataat: 128,relative; content:!"|0d|"; within: 128;sid:20221031;)
|
|
|
|
|
|
|
The National Institute of Standards and Technology (NIST) has The finalized report, Digital Details, including a link to the final version of the report, Read More
|