| The NJCCIC observed multiple Telephone-Oriented Attack Delivery (TOAD) emails targeting New Jersey State employees. Threat actors use email spoofing to make the email appear to come from the legitimate robinhood[.]com. The email header information reveals the sender’s hostname as v[number][.]megaserve[.]de, a domain used by netcup. This legitimate German web hosting provider assigns default names to their Virtual Private Servers (VPS). In this TOAD campaign, threat actors utilize an inexpensive VPS to spoof Robinhood in the “From” field to send thousands of emails. Although they successfully spoofed the Robinhood domain, the threat actors cannot hide the server that sent the emails. The threat actors rely on their targets to see “Robinhood” and not the megaserv[.]de server name hidden in the background. |
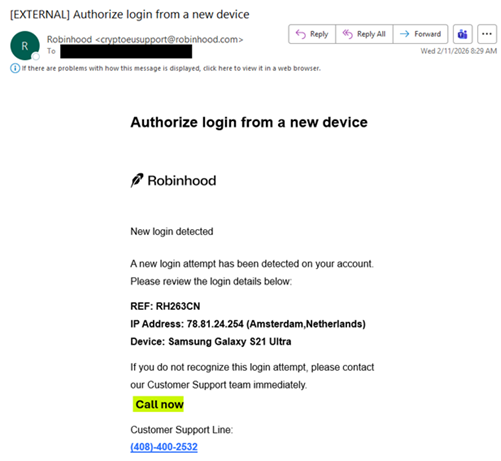
| These urgent emails impersonate Robinhood and claim that a new login attempt has been detected on the target’s account. They include a phone number to call Customer Support if the login is not recognized. If called, threat actors trick their targets into divulging sensitive information or downloading remote access software to commit further malicious activity. |
| Legitimate Robinhood phone support is only available through a callback request made inside the official app or website. They will send a push notification when you are next in line, with the exact phone number a representative will call you from, to ensure security and verify it on your caller ID. Robinhood will never ask you to call a phone number to “authorize” a new device, ask for your password or multi-factor authentication (MFA) code, or request that you download software or transfer funds. |
| Recommendations |
| Exercise caution with communications from known senders or legitimate platforms. Navigate directly to legitimate apps or websites and verify before submitting account credentials, providing personal or financial information, or downloading files. Enable MFA and keep systems and browsers up to date. If threat actors gain remote access, disconnect from the internet and run anti-virus/anti-malware scans. If sensitive information was entered, change passwords for compromised accounts, use the “Log out of all other sessions” feature in the real Robinhood app, monitor for unauthorized activity, and review the Identity Theft and Compromised PII NJCCIC Informational Report for additional recommendations and resources. Forward the entire email (including headers) to report this phishing scam to Robinhood (reportphishing@robinhood.com) and report abuse to the hosting provider (abuse@netcup.de). Report malicious cyber activity to the NJCCIC and the FBI’s IC3. |