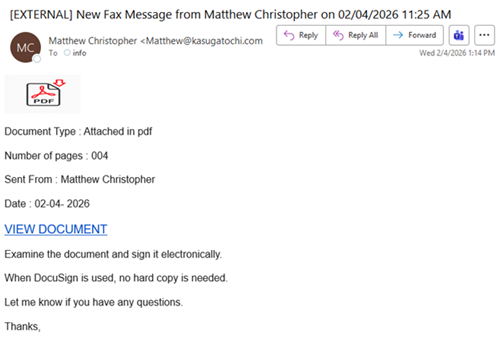
| As tax season is underway, the NJCCIC has already observed multiple tax and Internal Revenue Service (IRS) phishing campaigns in the past month, utilizing legitimate cloud services to host malicious files and targeting New Jersey State employees. In the above campaign, cyber threat actors send phishing emails disguised as fax messages in Adobe PDF format that needed to be examined and signed electronically via Docusign. If the “VIEW DOCUMENT” link is clicked, users are directed to a Docusign link hosting a JavaScript file called “2025_Matthew_taxdocs.pdf.” If executed, it will download and install the XWorm malware, a Remote Access Trojan (RAT) capable of gaining remote and persistent access, stealing data, and deploying ransomware. In a similar campaign, the phishing emails appear to come from Intuit QuickBooks and claim to be Docusign documents in need of review. If the link is clicked, users are first directed to a CAPTCHA screen and then to a Microsoft authentication page that harvests user credentials (usernames and passwords), multi-factor authentication (MFA) codes, and associated session cookies. |
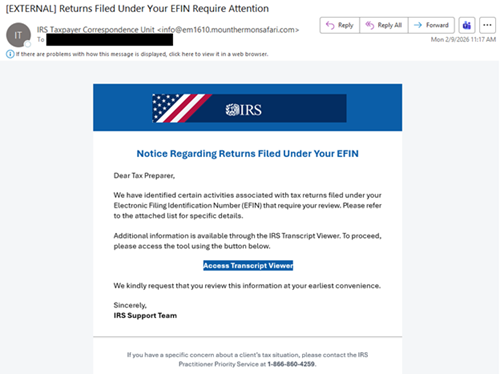
| In a separate campaign, cyber threat actors send messages purporting to be from the “IRS Taxpayer Correspondence Unit.” However, the sender’s email address does not include the IRS or tax-related terms. The messages claim to identify certain activities associated with the user’s Electronic Filing Identification Number (EFIN) that require review, attempting to convince the user to click the “Access Transcript Viewer” link. If clicked, users are directed to a link that abuses the legitimate Amazon Web Services to host phishing pages and malicious files. The URL leads to an “.src” file named “Access-EfinViews64-offline” that, if executed, installs the SimpleHelp remote monitoring and management (RMM) tool. This tool provides remote access to user devices and grants the cyber threat actors the ability to steal data from systems. |
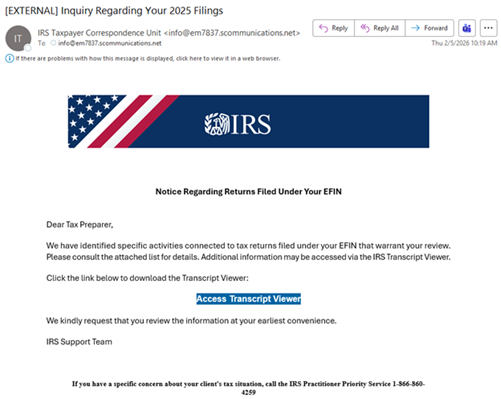
| Cyber threat actors also used the same template from the previous IRS campaign, but changed specific attributes and legitimate cloud services. For example, the sender’s email address in the above image is similar to the one used in the last campaign, but with a different domain (communications[.]net). Additionally, the same sender’s email address may be used in the “To” field, while the intended targets are in the “BCC” field. Other emails claim to come from “IRS Taxpayer Services Division” (servicedesk[@]irs[.]irsfilingtax[.]com), “IRS Audit and Records Department” (servicedesk[@]irs[.]irstaxportal[.]com), and “Internal Revenue Service (IRS) <irs[@]service[.]govdelivery[.]com> (donotreply[@]stateassist-irsrefundhub[.]com). Also, cyber threat actors use trivial subject lines, such as “Inquiry Regarding Your 2025 Filings,” or create urgent ones like “Immediate Attention Needed: IRS Review of Submitted Returns,” “Critical: Immediate Review of 2024 Tax Year Filings,” and “Urgent: Action Required for 2024 Tax Year Returns.” Furthermore, like the AWS Service link, cyber threat actors may also direct targeted users to a legitimate Bitbucket URL hosting a malicious file that installs the ScreenConnect or N-able RMM tool. These tax and IRS campaigns aim to gain remote access to the target’s device, maintain persistence, exfiltrate data, and deploy ransomware. |