APT44, also known as Sandworm, FROZENBARENTS, Seashell Blizzard, and Voodoo Bear, is a Russian state-sponsored cyber group attributed to GRU Unit 74455. APT44 has significantly evolved its operations in recent years, expanding from traditional cyber espionage into a full-spectrum capability encompassing sabotage, psychological operations, and battlefield support. Its campaigns have targeted Ukraine and NATO countries, with a growing focus on critical infrastructure such as energy, water, and telecommunications.
APT44’s operations increasingly leverage a combination of custom wiper malware, “living-off-the-land” (LOTL) techniques, and publicly available tools to conduct destructive attacks while minimizing attribution and detection. The group has also employed hacktivist personas and false-flag operations to obscure its involvement and sow confusion in the information space.
This shift reflects a broader strategic trend in Russian cyber doctrine, where cyber operations are fully integrated into military campaigns and geopolitical influence efforts. As hybrid conflict becomes the norm, organizations supporting critical functions must prepare not just for espionage, but pre-positioning and sabotage by highly capable actors like APT44.
Key Points
- APT44 is a Russian state-sponsored cyber sabotage and espionage group linked to GRU Unit 74455, known for targeting Ukraine, NATO member states, and global critical infrastructure.
- The group has expanded its mission set from military intelligence collection to including destructive operations, information warfare, and support for military campaigns.
- APT44 employs a hybrid toolkit combining custom wiper malware, commodity RATs, and LOTL techniques, often delivered through supply-chain compromises, phishing, and edge device exploitation.
- APT44’s tactics enable it to operate covertly within civilian networks, undermining traditional perimeter defenses and increasing operational risk for infrastructure operators, especially in energy, water, and telecom sectors.
Risk Assessment
The NJCCIC has assessed that APT44 poses a significant and escalating threat to organizations that operate critical infrastructure, higher education networks, and government systems. By deploying destructive malware, targeting industrial control systems, and integrating LOTL techniques with newer cloud and AI-enabled capabilities, the group can achieve both immediate disruption and sustained covert access.
This evolution is particularly concerning for organizations with operational technology dependencies and hybrid cloud environments, where visibility into lateral movement, identity abuse, and process manipulation are often limited. APT44 has previously conducted highly disruptive attacks such as NotPetya and Industroyer2 against similar targets, and its malware families have been observed exploiting vulnerabilities common across enterprise and industrial systems.
These tactics align with persistent weaknesses in cloud security, OT/IT integration, and incident response readiness, increasing the likelihood of severe service disruption, data loss, or reputational harm. The group’s destructive mandate, combined with its ability to blend disruption with stealthy persistence, underscores the urgent need for enhanced detection, network segmentation, and resilience planning against APT44 campaigns.
Threat Actor Summary
APT44, associated with the GRU’s Unit 74455 (Sandworm), primarily targets government, energy, critical infrastructure, technology, and education sectors in countries such as Ukraine, the United States, NATO members, and other Western allies. Since 2009, the group has been actively tracked by the cybersecurity community and is regarded as one of Russia’s most destructive and disruptive cyber units, supporting Moscow’s military and geopolitical objectives.
Technical Analysis
Tactics, Techniques, & Procedures
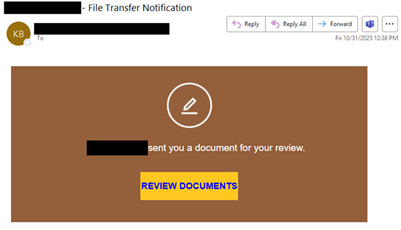
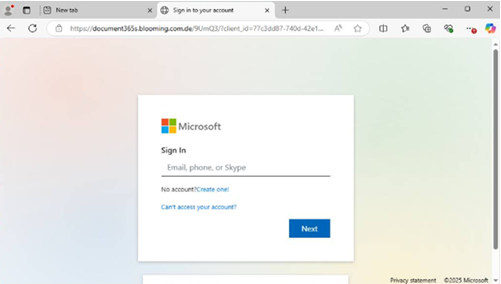
APT44 is known for its destructive and disruptive cyber operations in support of Russian military objectives. The group often gains access through spearphishing campaigns, exploitation of edge vulnerabilities, and supply chain compromises. They also employ LOTL techniques to blend into normal network activity and establish persistence.
Once inside, APT44 deploys custom malware families such as NotPetya, BlackEnergy, Industroyer, and Industroyer2, designed to wipe data, disrupt systems, or directly manipulate industrial control systems (ICS). Unlike espionage-focused groups, APT44 frequently times operations with kinetic military actions and leverages wipers, ICS-targeting tools, and destructive payloads to maximize impact.
Infrastructure
APT44 maintains a diverse and adaptable infrastructure to support its operations. This includes the use of compromised servers, hijacked domains, and VPNs for command-and-control (C2). They have also leveraged hardcoded infrastructure within destructive malware, creating global spillover effects, as seen in the NotPetya campaign. In recent activity, APT44 has increasingly relied on compromised network devices and legitimate administrative tools to maintain access and facilitate attacks.
Victims
APT44’s targeting closely aligns with Russia’s military and geopolitical priorities, focusing on disruption rather than espionage. Victims have included critical infrastructure operators, energy providers, higher education institutions, and government agencies, particularly those supporting Ukraine or NATO allies. Their operations are designed to undermine stability, cause economic damage, and erode confidence in Western institutions.
Target Sectors
- Government and Defense Institutions
- Energy and Critical Infrastructure (including ICS/SCADA systems)
- Higher Education and Research
- Technology and Telecommunications
- Media and Olympics
Geographic Focus
- Ukraine
- United States
- NATO Member States
- European Union Countries
- Western Allies supporting Ukraine
Attribution
APT44 has been widely attributed to the Russian GRU’s Main Center for Special Technologies (Unit 74455), commonly referred to as Sandworm. This attribution is supported by forensic evidence, including the reuse of destructive malware families, infrastructure overlaps, operational timing aligned with Russian military campaigns, and strategic targeting consistent with Russian state objectives. The group’s working patterns, Russian language artifacts, and repeated coordination with broader GRU operations reinforce its role as a core offensive cyber unit of the Russian state.