Great blog post By Microsoft
The shift toward hybrid work environments has led to a significant increase in cloud service adoption in recent years. In fact, on average, organizations now use 147 public cloud services across SaaS, PaaS, and IaaS, compared with just 38 services in 2020*. While cloud services offer many benefits, they also raise concerns about the security of sensitive data that can flow and be stored everywhere without a clear perimeter. The loss of sensitive data remains the top security concern in cloud services* for IT and security professionals, and it’s crucial to have integrated data security solutions that can protect sensitive data in multicloud environments at scale to address these challenges effectively.
It’s essential to keep in mind that data doesn’t move by itself, it’s people who move and interact with data, and that’s where the majority of data security risks stem from. According to research by Gartner®, “90% of employees who admitted undertaking a range of unsecure actions during their work activities knew that their actions would increase risk to the organization and undertook the actions anyway for speed and convenience.**” This finding reinforces what we discussed in the previous blog post: the most significant cybersecurity risks often come from insiders within your organization. Therefore, managing insider risks related to data is crucial when it comes to ensuring data security in different environments.
Today, we are pleased to announce new features to help tailor the Insider Risk Management solution for your organization’s use across multiple environments:
- Bring your own detections to manage insider risks across multiple environments holistically
- Prevent high risk users from pasting sensitive data into browser applications
- Customize insider risk detections for different user groups
- Bolster your investigation efforts with new enhancements
- Get started easily with insider risk analytics and enhanced quick policies
Microsoft Purview Insider Risk Management correlates various signals to identify potential malicious or inadvertent insider risks, such as IP theft, data leakage, and security violations. Insider Risk Management enables customers to create policies to manage security and compliance. Built with privacy by design, users are pseudonymized by default, and role-based access controls and audit logs are in place to help ensure user-level privacy.
Bring your own detections to manage insider risks across multiple environments holistically
With our new bring your own detections feature coming into public preview in the next few weeks, admins with the right permissions can bring in user activity signals from multiple sources, extending the power of the solution to a broader set of environments.
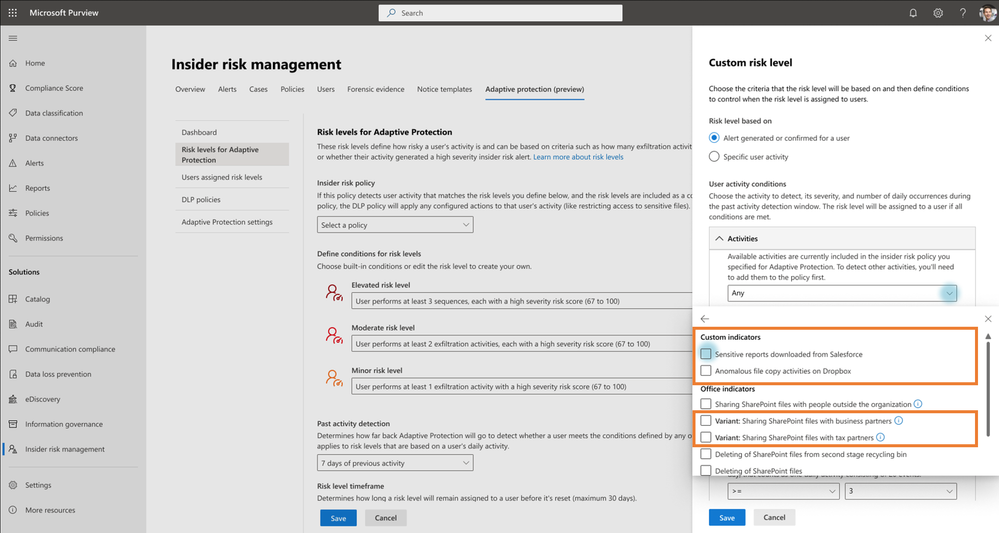
For instance, you can import events from CRM systems, such as Salesforce, including signals like sharing and exporting reports that may be considered risky and therefore could lead to a data security incident. These signals can then be used as custom indicators in insider risk policies and combined with other native signals to give organizations comprehensive detection and understanding of potential insider risks across their broader environments.

As a result, all the insider risk indicators can be viewed in one place on the user activity chart. In the following scenario, for example, the custom indicator, sensitive reports downloaded from Salesforce, is weaved into the user activities timeline, which provides security teams with a holistic view of a potential data security incident across applications.

In addition, you can also leverage these indicators to configure user’s risk levels for Adaptive Protection, the capability we announced in February that helps dynamically tailor Microsoft Purview Data Loss Prevention policies to mitigate data security risks. For example, you can use the custom indicator, “sensitive reports downloaded from Salesforce”, as a condition, to define the elevated risk level and automatically add users who match the conditions to a strict DLP policy.
Prevent high risk users from pasting sensitive data into browser applications
In addition to bringing in detections from other applications, we are also announcing a new Microsoft Data Loss Prevention capability to help organizations prevent the pasting of sensitive data into supported web browsers. To balance productivity, customers can leverage this new feature with Adaptive Protection to prevent certain actions from high-risk users.
For example, a user who has engaged in risky data exfiltration activities will be identified as a high-risk user in Adaptive Protection. If this high-risk user then attempts to paste sensitive information into a web browser, they will be blocked from doing so. Whereas a low-risk user can paste sensitive data into a web browser and provide justification for doing so. You can learn more about configuring paste to browser in Data Loss Prevention here and how to leverage Adaptive Protection for this capability here.
Tailor insider risk detections for your different user groups
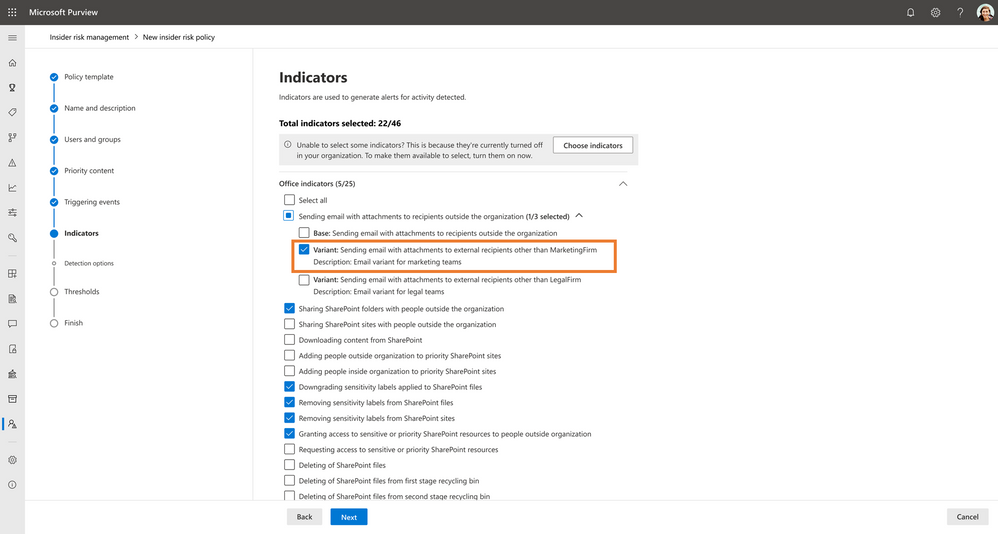
While Insider Risk Management offers dozens of ready-to-use indicators, the detection of insider risks may not be a one-size-fits-all solution for all users in an organization. For example, the marketing and legal departments might need to send emails to different external domains, such as marketing agencies versus outside legal counsel, to collaborate and complete their tasks.
Coming soon in a few weeks, organizations can add variants to the built-in insider risk indicators and tailor detections for different sets of users. In the scenario above, administrators can configure two variants for the “sending email with attachments to recipients outside the organization” indicator, allowing marketing and legal teams to have a different set of allowed domains that won’t generate alerts:
- Sending email with attachments to external recipients other than MarketingFirm – will only generate alerts when users send emails to an external domain that is not part of the MarketingFirm allowed list
- Sending email with attachment to external recipients other than LegalFirm – will only generate alerts when users send emails to an external domain that is not part of the LegalFirm allowed list
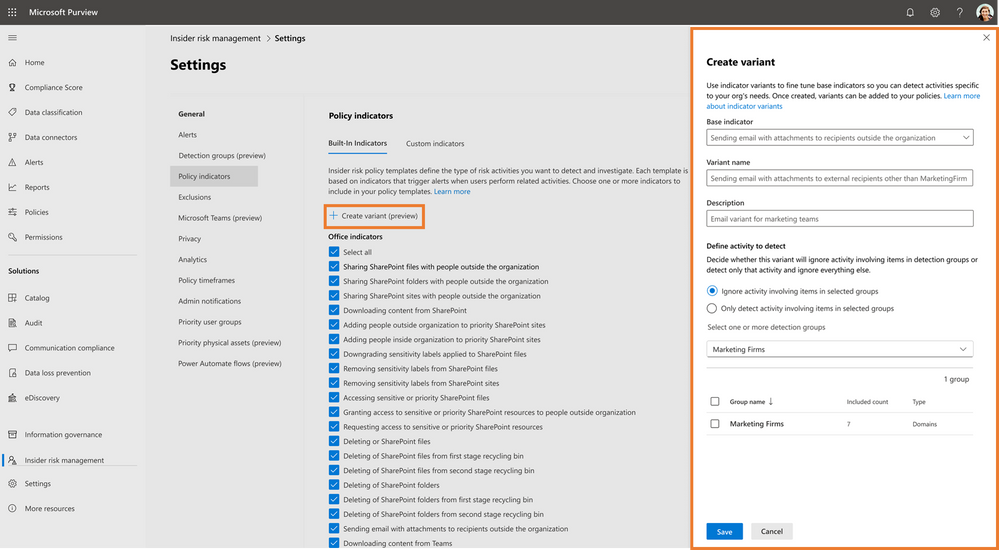
This customization empowers security teams to create tailored insider risk policies for each team and reduce the number of false positives, leading to more accurate detection of insider risks. Similar to the bring-your-own-detections announcement above, security teams can also use these variants to configure Adaptive Protection to dynamically apply DLP policies based on user’s risk levels.
Bolster your investigation efforts with new enhancements
Managing insider risks is a collaborative effort that often involves a team of analysts and investigators working together to review and prioritize alerts. Recognizing the importance of teamwork, we are excited to announce the rollout of a few enhancements that will help bolster your security team’s investigation efforts, while preserving end user privacy with pseudonymization.
Coming soon in public preview, security teams can easily assign alerts or cases to a dedicated owner to help clarify ownership and ensure accountability. Additionally, each alert and case will be assigned a static and unique ID, making it easier to communicate when pseudonymization is on. These improvements can help enable better tracking and communication among team members.

When investigating an insider risk alert, analysts typically use various filters and columns, such as date, workload, and sensitivity label, in the activity explorer to gain insights into risky activities that could potentially result in data security incidents. To further streamline this process and enhance efficiency when working on recurring activities, we are introducing the new saved views feature in the activity explorer, available in public preview in a few weeks. This feature allows you to access a previously configured combination of filters and columns with just one click, eliminating the need to manually set them up each time.
Furthermore, the activity explorer’s export limit will increase from 10K to 100K records. This update will benefit organizations that prefer exporting insights of user activities that may lead to data security incidents to a CSV file, as they now can filter, sort, or pivot a bigger data set more conveniently.
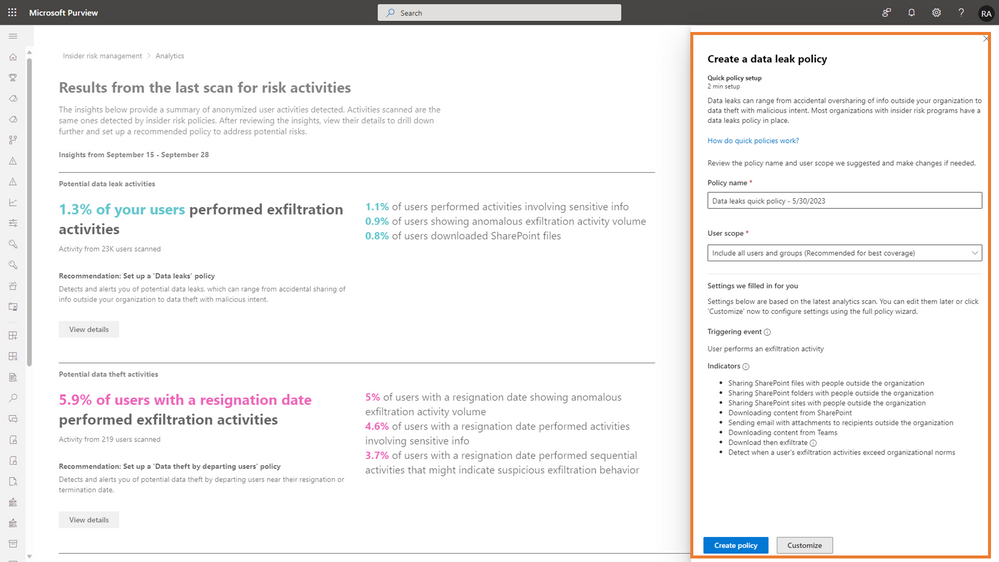
Get started easily with insider risk analytics and enhanced quick policies
To help jump start your journey into leveraging the power of Insider Risk Management in your organization, we announced the public preview of the one-step policy creation in a blog post in July 2022. During the preview, we learned and improved the quick policy defaults tailored to various tenants, ensuring that you can start identifying risky activity in a healthy state while working on optimizing your policies over time. We’re thrilled to announce that this feature will become generally available to both commercial and government cloud customers in the next few weeks.
Think of the one-step policy creation as a shortcut that leads you to the right path. Security teams can easily set up a policy in just one click, based on the aggregated insights from Analytics in Insider Risk Management. It evaluates your organization’s insider risk posture, and then based on that, recommends a default set of policy configurations and thresholds. The quick policies give you a solid starting point, so you can begin receiving alerts and insights and finetune the policies further.
Explore more Insider Risk Management resources
- Learn more about Insider Risk Management in our technical documentation.
- Insider Risk Management is part of the Microsoft Purview suite of solutions designed to help organizations manage, govern and protect their data. If you are an organization using Microsoft 365 E3 and would like to experience Insider Risk and other Purview solutions for yourself, check out our E5 Purview trial.
- If you own Insider Risk Management and are interested in learning more about Insider Risk Management, leveraging Insider Risk Management to understand your environment, or building policies for your organization or investigate potential risky user actions, check out the resources available on our “Become an Insider Risk Management Ninja” resource page.
– Erin Miyake, Principal Product Manager, Microsoft Purview Insider Risk Management