Security is an essential component of High-Performance Computing Register
|
Security is an essential component of High-Performance Computing Register
|
The NIST AI RMF is a framework to manage risks to individuals,
organizations, and society associated with artificial intelligence (AI). The
Framework is intended for voluntary use to improve the ability to
incorporate trustworthiness considerations into the design, development, use,
and evaluation of AI products, services, and systems. It has been developed
through a consensus-driven, open, transparent, and collaborative process.
Sign up to
receive email notifications about NIST’s AI activities.
At Microsoft, our mission is to help you achieve more, so we’re making certifications, and the resources to learn, prepare, and get certified, free to all eligible students, starting with fundamentals certifications through June 2023.
Technology is changing the future of work. In every industry, employers expect interns and recent graduates to have the digital capabilities they need to thrive in a modern—often hybrid or remote—working environment. While digital skills are a great start, students also need skills in data, AI, and cloud technologies to make the most of every opportunity. Earning a Microsoft Certification does more than just build technical skills; certifications can help you stand out, gain confidence, and even get paid more1. Microsoft Certifications also validate your skills and abilities, while proving your commitment to learning the latest technologies.
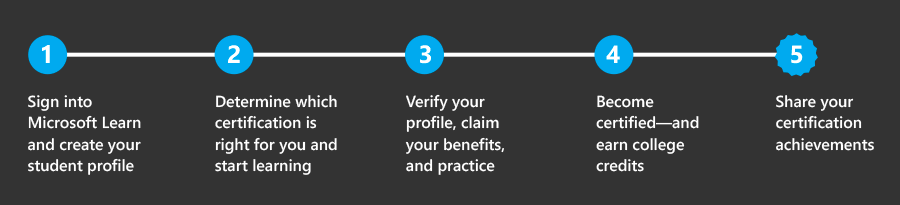
Microsoft Learn is the place to start and customize your learning journey with up-to-date content developed by experts and a variety of resources. Master new skills with a comprehensive collection of training options that empower you to learn in a style that fits you best. Sign into Microsoft Learn and create your student profile to track your progress on learning activities, create and share content collections, accrue points and achievements, use free Azure resources, and get personalized recommendations.
Microsoft Certifications are based on industry analysis of specific jobs and roles and are continually updated to reflect the latest technologies. They enhance your credibility, giving you the professional advantage of globally recognized, industry-endorsed skills. Earning a Microsoft Certification enables employers and peers to recognize your talent and experience—and can help you build the technical skills you need to succeed in today’s fast-paced, digital world.
Microsoft Certifications start with foundational skills and move into the deeper technical skills you will need to perform industry roles. Microsoft Certifications also cover technical topics from Azure to AI, to data analytics and cybersecurity.
| Exam | Self-paced online content | Exam cram |
|---|---|---|
| AZ-900: Microsoft Azure Fundamentals | ✔ | ✔ |
| DP-900: Microsoft Azure Data Fundamentals | ✔ | ✔ |
| AI-900: Microsoft Azure AI Fundamentals | ✔ | ✔ |
| SC-900: Microsoft Security, Compliance, and Identity Fundamentals | ✔ | ✔ |
| PL-900: Microsoft Power Platform Fundamentals | ✔ | ✔ |
| MB-910: Microsoft Dynamics 365 Fundamentals (CRM) | ✔ | ✘ |
| MB-920: Microsoft Dynamics 365 Fundamentals (ERP) | ✔ | ✘ |
| MS-900: Microsoft 365 Fundamentals | ✔ | ✘ |
As part of this initiative, Microsoft provides exam vouchers to eligible students so that they can take Fundamentals exams for free.
Fundamentals certifications are a great way to start your certification journey. Validate your foundational understanding with mixed concepts and apply what you learn about Microsoft technologies—no area experience required. Fundamentals also give you a springboard into deeper, role-based learning paths and certifications.
You just need to verify your enrollment at an accredited academic institution to claim the benefits.
Note
This student initiative is managed by Cloud Ready Ltd. on behalf of Microsoft. When you access the Cloud Ready website using your Microsoft Account credentials, your use of that website and any collection of personal data will be governed by the Cloud Ready Privacy Policy.
Get even more credit for your new skills. Students can now receive college credits for passing Microsoft Exams and earning Microsoft Certifications. Read the story of students Sam Jones and Jason Powell, who saved money and completed their degrees faster with college credits they earned as a result of their Microsoft Certifications. Review the tools and resources they used so you can do the same.
Tip
We’re committed to ensuring that every person who’s interested in taking Microsoft Certification exams can do so in a way that is fair and accurately reflects their skills and abilities. Learn more about requesting accommodations.
Celebrate your success! You worked hard to earn your certification. Now, be sure to share your new achievement with the world via a digital badge.
Showcasing your professional achievements may help you get noticed by potential employers. When you share your digital badge on popular sites, such as LinkedIn, Facebook, and Twitter, or when you embed it into your resume, personal website, or email signature, anyone who sees your badge will immediately recognize it as a trusted Microsoft validation of your achievement.
Learn more about how to claim your badge and showcase your skills and certifications
This is a post from Microsoft.
On January 13th, Windows Security and Microsoft Defender for Endpoint customers may have experienced a series of false positive detections for the Attack Surface Reduction (ASR) rule “Block Win32 API calls from Office macro” after updating to security intelligence builds between 1.381.2134.0 and 1.381.2163.0. These detections resulted in the deletion of files that matched the incorrect detection logic primarily impacting Windows shortcut (.lnk) files.
There is no impact for customers who do not have the “Block Win32 API calls from Office macro” rule turned on in block mode or did not update to security intelligence update builds 1.381.2134.0, 1.381.2140.0, 1.381.2152 and 1.381.2163.0.
For currently impacted customers: what do I need to do?
Impacted customers will need both the updated security intelligence build and follow the process to recover start menu and taskbar shortcuts.
The updated security intelligence build
Customers should update to build 1.381.2164.0 or later. Customers utilizing automatic updates for Microsoft Defender antivirus do not need to take additional action to receive the updated security intelligence build. Enterprise customers managing updates should download the latest update and deploy it across their environments. The security intelligence build does not restore deleted shortcuts. Instructions on how to restore those are immediately below. If you turned “Block Win32 calls from Office macros” into audit mode per prior guidance you can now safely turn on block mode.
To recover deleted start menu and taskbar shortcuts
Microsoft has confirmed steps that customers can take to recreate start menu links for a significant sub-set of the affected applications that were deleted.
Version 4.0 is now streamlined so the script will perform all the actions including running the MpRecoverTaskbar.exe and is better equipped to handle errors. This script also provides additional checks that help recover more shortcuts and links. For more details click here.
1/ Download both AddShortcuts.ps1 and MpRecoverTaskBar.exe and select from the following options:
Option A/ If you are using System Center Config Manager or Group Policy Object Editor or third-party tools then deploy both files and run the command “powershell -ep bypass -file .AddShortcuts.ps1 -MpTaskBarRecoverUtilDownload=false” as Administrator.
Option B/ If you are using Intune or no management tool then deploy AddShortcuts.ps1 and run the command “powershell -ep bypass -file .AddShortcuts.ps1” as Administrator. This will automatically download MPTaskBarRecover.exe from the Microsoft download center onto the user’s machine and run the script. Detailed instructions on how to deploy the script using Microsoft Intune are here.
2/ The changes will come into effect after users logout and login to their accounts.
3/ The MPRecoverTaskbar.exe can be run multiple times on end-user machines if necessary. If end-users are missing taskbar icons after completing this process, then try running it a second time from %windir%MPRecoverTaskbar.exe in the user context.
The script requires PowerShell 5.x and does not currently support PowerShell 7.x.
Version 4.0 includes all the improvements from Version 3.0: restores from Volume Shadow Copy Service by default, recovers .URL files in the user’s profile’s Favorites and Desktop directories, if those URL files exist in the Volume Shadow Copy Service, contains improvements for non-English language machines, while adding improved error handling and additional checks that help recover more shortcuts and links.
To add programs to the script: edit the $program variable and add a new line with the name of the application lnk and the executable.
For customers that prefer manual steps rather than the script running an application repair on affected applications will recreate deleted links. Users can run the Application Repair functionality for programs including Microsoft 365, Microsoft Edge, and Microsoft Visual Studio.
To repair an application, follow these instructions:
Verifying environment impact
Customers can verify the impact of this issue in their environment through the following advanced hunting queries (AHQs):
This AHQ can retrieve all block events from devices with ASR rule “Block Win32 API calls from Office macro” enabled on “Block” mode, run this query.
DeviceEvents
| where Timestamp >= datetime(2023-01-13)
| where ActionType contains “AsrOfficeMacroWin32ApiCallsBlocked”
| extend JSON = parse_json(AdditionalFields)
| extend isAudit = tostring(JSON.IsAudit)
| where isAudit == “false”
| summarize by Timestamp, DeviceName, DeviceId, FileName, FolderPath, ActionType, AdditionalFields
| sort by Timestamp asc
This AHQ can retrieve all events from devices with ASR rule “Block Win32 API calls from Office macro” enabled on “block” and “audit” mode, run this query.
DeviceEvents
| where Timestamp >= datetime(2023-01-13)
| where ActionType contains “AsrOfficeMacroWin32ApiCallsBlocked”
| summarize by Timestamp, DeviceName, DeviceId, FileName, FolderPath, ActionType, AdditionalFields
| sort by Timestamp asc
This AHQ can retrieve the device count with this ASR rule “Block Win32 API calls from Office macro” enabled and if the number is exceeding 10K, run this query.
DeviceEvents
| where Timestamp >= datetime(2023-01-13)
| where ActionType contains “AsrOfficeMacroWin32ApiCallsBlocked”
| summarize deviceCount = dcount(DeviceId)
| extend IsMoreThanTenThousand = iif(deviceCount> 10000, True, False)
Advanced Hunting Queries are not available in Defender for Endpoint P1 which is also included in E3 and A3 or in Defender for Business. To identify affected machines run the script here on individual user machines.
FAQ
Additional questions are addressed in the FAQ document.
Ever wanted to do a practice test before sitting for a Microsoft certification? You are in luck as Microsoft is starting to offer free practice tests for Microsoft certifications directly on Microsoft Learn!
Working on your certification goals and looking for practice tests? Take the online assessment directly from Microsoft Learn. Keep an eye out for the practice assessment link on the exam pages! For example it is now available for the SC-900 exam. https://learn.microsoft.com/en-us/certifications/exams/sc-900/
or
With Microsoft Learn, anyone can master core concepts at their speed and on their schedule. Whether it’s a single module to learn about a core task or exploring a topic fully through a collection of related modules.
There’s no cost to renew your certification, just make sure you pass the online assessment before your certification expires. Fundamentals certifications do not expire.
|
|
Cybersecurity Framework 2.0 Concept Paper:
The NIST Cybersecurity Framework (CSF) helps organizations better
understand, manage, reduce, and communicate cybersecurity risks. NIST is
updating the CSF to keep pace with the evolving cybersecurity landscape.
The CSF 2.0 Concept Paper released today outlines
more significant potential changes in the CSF. It is informed by extensive
feedback in response to the NIST Cybersecurity Request for
Information and the first workshop on
CSF 2.0. NIST
is publishing this concept paper to gain additional input before issuing a
draft CSF 2.0 this Summer. Please share feedback by March 3,
2023,via cyberframework@nist.gov.
Upcoming Events:
The Concept Paper will be discussed at two upcoming events:
On December 5, 2022, the National Cybersecurity Center of Excellence
(NCCoE) released for public comment the preliminary draft of NIST Special
Publication (SP) 1800-36A: Executive Summary, Trusted Internet of Things (IoT) Device Network-Layer
Onboarding and Lifecycle Management. The public comment period
is open until February 3, 2023.
Provisioning network credentials to IoT devices in an untrusted
manner leaves networks vulnerable to having unauthorized IoT devices connect to
them. It also leaves IoT devices vulnerable to being taken over by unauthorized
networks. Instead, trusted, scalable, and automatic mechanisms are needed to
safely manage IoT devices throughout their lifecycles, beginning with secure
ways to provision devices with their network credentials—a process known as trusted network-layer onboarding.
Trusted network-layer onboarding, in combination with additional device
security capabilities such as device attestation, application-layer onboarding,
secure lifecycle management, and device intent enforcement could improve the
security of networks and IoT devices.
This draft practice guide aims to demonstrate how organizations
can protect both their IoT devices and their networks. The NCCoE is
collaborating with product and service providers to produce example
implementations of trusted network-layer onboarding and capabilities that
improve device and network security throughout the IoT-device lifecycle to
achieve this.
The public comment period for this draft is open until February 3,
2023. See the publication details for a copy of the
draft publication and comment instructions.
The automotive industry is facing significant challenges from
increased cybersecurity risk and adoption of AI and opportunities from rapid
technological innovations. NIST is setting up this community of interest (COI)
to allow the industry to discuss, comment, and provide input on the work that
NIST is doing which will affect the automotive industry. Topics can include:
The COI is open and will provide a way for NIST to obtain comments
and feedback from the automotive industry. For example, NIST may ask the COI to
comment on publications; assist in developing use cases; and provide insight
into cybersecurity challenges of innovative technologies.
Industry, government and academics are all welcome to join.
To sign up for the Automotive Cybersecurity COI, please email autosecCOI@nist.gov
Questions may be sent to Autoseccoi-inquiry@nist.gov
NIST is announcing the initial public drafts of NIST SP 800-157r1
(Revision 1), Guidelines for
Derived Personal Identity Verification (PIV) Credentials,
and NIST SP 800-217, Guidelines for
Personal Identity Verification (PIV) Federation. These
two SPs complement Federal Information Processing Standard (FIPS) 201-3,
which defines the requirements and characteristics of government-wide
interoperable identity credentials used by federal employees and contractors.
NIST will introduce both draft documents at a virtual workshop on February 1,
2023. Please see the workshop homepage
to register and attend the virtual event.
The public comment period for both draft publications is open
through March 24, 2023. See the publication details
for NIST SP 800-157r1
and NIST SP 800-217
to download the drafts and find instructions for submitting comments.
NOTE: A call for
patent claims is included on page iii of each draft. For additional
information, see the Information Technology Laboratory (ITL) Patent Policy –
Inclusion of Patents in ITL Publications.
Ransomware continues to be one of the most prevalent and impactful threats affecting organizations, with attackers constantly evolving their techniques and expanding their tradecraft to cast a wider net of potential targets. This is evident in the range of industries, systems, and platforms affected by ransomware attacks. Understanding how ransomware works across these systems and platforms is critical in protecting today’s hybrid device and work environments.
This blog provides details from our analysis of known ransomware families affecting macOS devices. As in other platforms, the initial vector of Mac ransomware typically relies on user-assisted methods like downloading and running fake or trojanized applications. It can, however, also arrive as a second-stage payload dropped or downloaded by other malware or part of a supply chain attack. Once running on a device, ransomware attacks usually comprise gaining access, execution, encrypting target users’ files, and notifying the target with a ransom message.
To perform these actions, malware creators abuse legitimate functionalities and devise various techniques to exploit vulnerabilities, evade defenses, or coerce users to infect their devices. We describe these techniques in detail below, based on our analysis of four Mac ransomware families: KeRanger, FileCoder, MacRansom, and EvilQuest. In particular, we take a deeper look at EvilQuest and one of its variants that had its ransomware component removed but was further improved with additional techniques and anti-analysis logic.
While these malware families are old, they exemplify the range of capabilities and malicious behavior possible on the platform. Building durable detections for these techniques will help improve defenses for devices and networks against ransomware and other threats. As with any security research in Microsoft, this in-depth analysis of malware techniques informs the protection we provide through solutions like Microsoft Defender for Endpoint on Mac. We’re sharing this information with the rest of the community as a technical reference that researchers can use and build upon to understand Mac threats and improve protections.
To read the Full article go here