Vulnerabilities in network components, architecture files, and developer tools have become increasingly popular attack vectors to gain access into secure networks and devices. External tools and products that are managed by vendors and developers can pose a security risk, especially to targets in sensitive industries. Attacks on software and hardware supply chains, like Log4J and SolarWinds, have highlighted the importance of visibility across device components and proactively securing networks. A report published by Recorded Future in April 2022 detailed suspected electrical grid intrusion activity and implicated common IoT devices as the vector used to gain a foothold into operational technology (OT) networks and deploy malicious payloads. While investigating the attack activity, Microsoft researchers identified a vulnerable component on all the IP addresses published as IOCs and found evidence of a supply chain risk that may affect millions of organizations and devices.
We assessed the vulnerable component to be the Boa web server, which is often used to access settings and management consoles and sign-in screens in devices. Despite being discontinued in 2005, the Boa web server continues to be implemented by different vendors across a variety of IoT devices and popular software development kits (SDKs). Without developers managing the Boa web server, its known vulnerabilities could allow attackers to silently gain access to networks by collecting information from files. Moreover, those affected may be unaware that their devices run services using the discontinued Boa web server, and that firmware updates and downstream patches do not address its known vulnerabilities.
In this blog, we detail the risks affiliated with vulnerable components, highlighting the Boa web server, and how we suspect these components could be exploited to target critical industries. We also discuss the difficulties with identifying these components in device supply chains. To provide comprehensive protection against such attacks, we offer detection information to identify vulnerable components and guidance for organizations and network operators to improve their security posture.
Investigating the attack activity
The attack detailed in the Recorded Future report was one of several intrusion attempts on Indian critical infrastructure since 2020, with the most recent attack on IT assets confirmed in October 2022. Microsoft assesses that Boa servers were running on the IP addresses on the list of IOCs published by Recorded Future at the time of the report’s release and that the electrical grid attack targeted exposed IoT devices running Boa.
Microsoft further identified that half of the IP addresses published by Recorded Future returned suspicious HTTP response headers, which might be associated with the active deployment of the malicious tool identified by Recorded Future. The combination of Boa and suspicious response headers was identified on another set of IP addresses, displaying similar behavior to those found by Recorded Future. While these IP addresses are not confirmed as malicious, we recommend they be monitored to ensure no additional suspicious activity. Users of Microsoft Defender Threat Intelligence will find these IP addresses in the portal labeled as block-listed or suspicious:
- 122[.]117[.]212[.]65
- 103[.]58[.]93[.]133
- 125[.]141[.]38[.]53
- 14[.]45[.]33[.]239
- 14[.]55[.]86[.]138
- 183[.]108[.]133[.]29
- 183[.]99[.]53[.]180
- 220[.]94[.]133[.]121
- 58[.]76[.]177[.]166
Investigating the headers further indicated that over 10% of all active IP addresses returning the headers were related to critical industries, such as the petroleum industry and associated fleet services, with many of the IP addresses associated to IoT devices, such as routers, with unpatched critical vulnerabilities, highlighting an accessible attack vector for malware operators. Most of the suspicious HTTP response headers were returned over a short timeframe of several days, leading researchers to believe they may be associated with intrusion and malicious activity on networks.
Since the report’s publication, Microsoft researchers tracking the published IPs hosts have observed that all IP addresses have been compromised by a variety of attackers employing different malicious methods. For example, some of the IP addresses were further leveraged to download a variant of the Mirai malware family shortly following the report’s release. Microsoft also found evidence that across different devices on the IP addresses, there were attempts to connect with default credentials through brute force methods and attempts to run shell commands. Microsoft continues to see attackers attempting to exploit Boa vulnerabilities beyond the timeframe of the released report, indicating that it is still targeted as an attack vector.
Boa widespread through SDKs
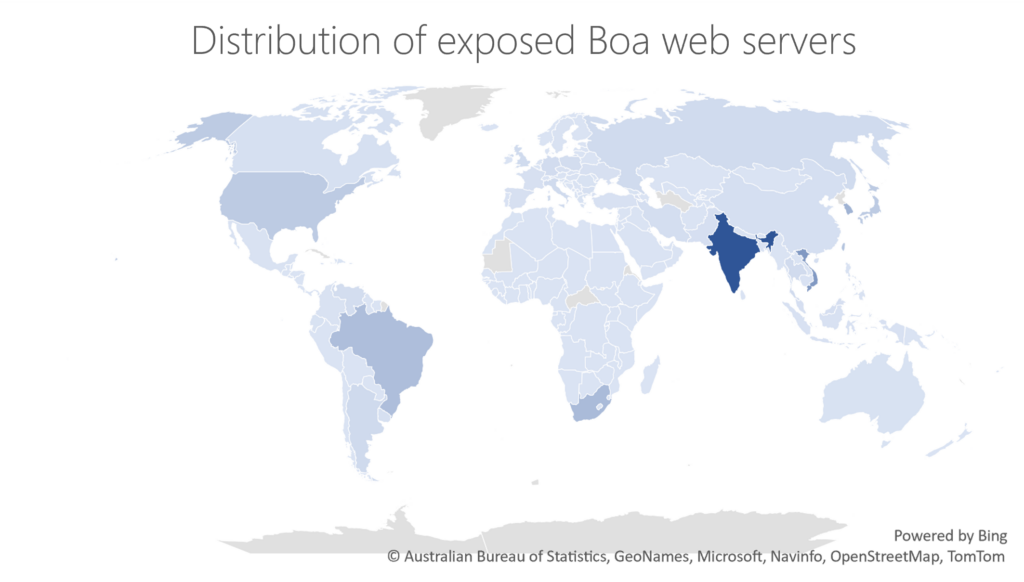
The Boa web server is widely implemented across a variety of devices, including IoT devices ranging from routers to cameras, and is often used to access settings and management consoles as well as sign-in screens. The popularity of Boa web servers is especially concerning as Boa has been formally discontinued since 2005. Data from the Microsoft Defender Threat Intelligence platform identified over 1 million internet-exposed Boa server components around the world over the span of a week, as depicted in the below figure:
Boa web servers remain pervasive in the development of IoT devices, one reason for this could be its inclusion in popular SDKs, which contain essential functions that operate system on chip (SOC) implemented in microchips. Vulnerable components like Boa and SDKs are often distributed to customers within devices, contributing to supply chain vulnerabilities. Popular SDKs like those released by RealTek, are used in SOCs provided to companies that manufacture gateway devices like routers, access points, and repeaters. Critical vulnerabilities such as CVE-2021-35395, which affected the digital administration of devices using RealTek’s SDK, and CVE-2022-27255, a zero-click overflow vulnerability, reportedly affect millions of devices globally and allow attackers to launch code, compromise devices, deploy botnets, and move laterally on networks.
While patches for the RealTek SDK vulnerabilities are available, some vendors may not have included them in their device firmware updates, and the updates do not include patches for Boa vulnerabilities. Boa servers are affected by several known vulnerabilities, including arbitrary file access (CVE-2017-9833) and information disclosure (CVE-2021-33558). These vulnerabilities may allow attackers to execute code remotely after gaining device access by reading the “passwd” file from the device or accessing sensitive URIs in the web server to extract a user’s credentials. Moreover, these vulnerabilities require no authentication to exploit, making them attractive targets.
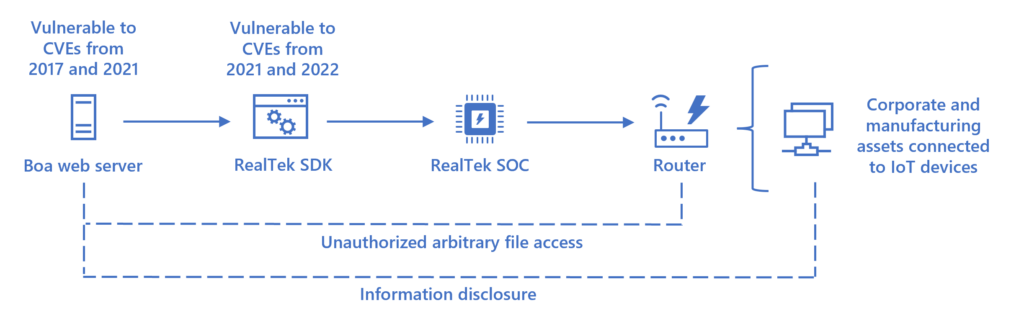
The popularity of the Boa web server displays the potential exposure risk of an insecure supply chain, even when security best practices are applied to devices in the network. Updating the firmware of IoT devices does not always patch SDKs or specific SOC components and there is limited visibility into components and whether they can be updated. The known CVEs impacting such components can allow an attacker to collect information about network assets before initiating attacks, and to gain access to a network undetected by obtaining valid credentials. In critical infrastructure networks, being able to collect information undetected prior to the attack allows the attackers to have much greater impact once the attack is initiated, potentially disrupting operations that can cost millions of dollars and affect millions of people.
Recommendations
As attackers seek new footholds into increasingly secure devices and networks, identifying and preventing distributed security risks through software and hardware supply chains, like outdated components, should be prioritized by organizations. This case displays the importance of proactive cyber security practices and the need to identify vulnerable components that may be leveraged by attackers.
Microsoft recommends that organizations and network operators follow best practice guidelines for their networks:
- Patch vulnerable devices whenever possible to reduce exposure risks across your organization.
- Utilize device discovery and classification to identify devices with vulnerable components by enabling vulnerability assessments, which identifies unpatched devices in the organizational network and set workflows for initiating appropriate patch processes with solutions like Microsoft Defender Vulnerability Management and Microsoft Defender for Endpoint with Microsoft Defender for IoT .
- Extend vulnerability and risk detection beyond the firewall with platforms like Microsoft Defender External Attack Surface Management. Customers can identify internet-exposed infrastructure running Boa web server components in their inventory and use the insights tile under the Attack Surface Summary dashboard to surface assets vulnerable to CVE-2017-9833. The insight can be found under High Severity Observations.
- Reduce the attack surface by eliminating unnecessary internet connections to IoT devices in the network. Apply network segmentation to prevent an attacker from moving laterally and compromising assets after intrusion. IoT and critical device networks should be isolated with firewalls.
- Use proactive antivirus scanning to identify malicious payloads on devices.
- Configure detection rules to identify malicious activity whenever possible. Security personnel can use our snort rule below to configure security solutions to detect CVE-2022-27255 on assets using the RealTek SDK.
alert udp any any -> any any (msg:"Realtek eCOS SDK SIP Traffic Exploit CVE-2022-27255"; content: "invite"; depth: 6; nocase; content: "sip:"; content: "m=audio "; isdataat: 128,relative; content:!"|0d|"; within: 128;sid:20221031;)
- Adopt a comprehensive IoT and OT solution like Microsoft Defender for IoT to monitor devices, respond to threats, and increase visibility in order to detect and alert when IoT devices with Boa are used as an entry point to a network and protect critical infrastructure.